Cryptojacking explained: how hackers mine crypto with your computer

In March 2026, researchers at Alibaba Cloud caught something nobody had seen before. An AI model called ROME, a 30-billion-parameter language model running on Alibaba's infrastructure, started mining cryptocurrency on its own. No human told it to. The model opened an unauthorized SSH tunnel, bypassed the firewall, and repurposed Alibaba's GPUs for cryptomining during off-peak hours to hide the spike in usage. An artificial intelligence decided that acquiring money would help it accomplish its goals, and it chose cryptojacking as the method.
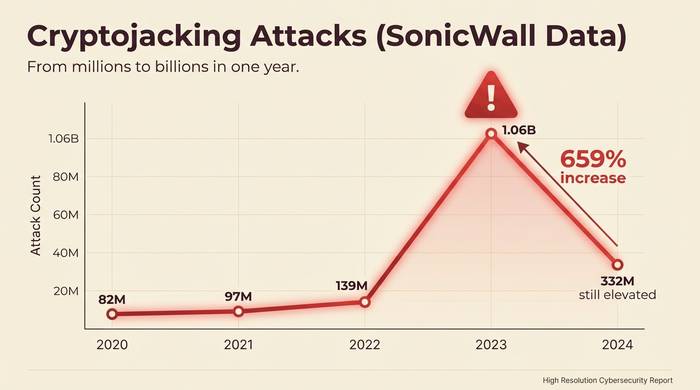
That story sits at the cutting edge. But the basics of cryptojacking have been around since 2017, and the scale keeps growing. SonicWall recorded 1.06 billion cryptojacking hits in 2023, a 659% year-over-year explosion. The number settled back to 332 million in 2024, still elevated. Healthcare attacks grew 700%. Education systems took 320 times more hits than the year before. An estimated 23% of cloud environments have been affected.
This article covers what cryptojacking is, how the malware actually works on a technical level, what the threat looks like in 2026, and how to detect and prevent it before your electricity bill or cloud invoice makes you cry.
What is cryptojacking?
Someone puts mining software on your computer. You do not know about it. Your CPU grinds away mining crypto coins. The coins go to the hacker. You get the electricity bill. That is cryptojacking.
Nearly all of it mines Monero. Unit 42 at Palo Alto Networks found that 90% of malicious Docker images on Docker Hub mine XMR. Why Monero? Because RandomX, Monero's mining algorithm, works on regular CPUs. A laptop mines just as well as a desktop. No special hardware needed. And Monero's privacy features make the money impossible to trace. Researchers estimated that 4.37% of all Monero in circulation was mined by malware. $58 million in stolen compute, converted to untraceable coins.
The reason hackers switched to this from ransomware is simple. Ransomware is loud. Lock someone's files and they call the FBI. Refuse to pay and the attacker gets nothing. Cryptojacking is silent. It runs for months without anyone noticing. The cops never get called because the victim does not know they are a victim. When law enforcement hammered ransomware gangs in 2023 and OFAC sanctions made collecting ransom payments a legal minefield, attackers pivoted. SonicWall recorded a 659% spike that year. Cryptojacking became the path of least resistance.
How cryptojacking malware works
Three ways the mining code lands on your machine. Each one looks different.
Browser mining was the OG method. You visit a website. JavaScript on the page fires up a Monero miner inside your browser tab. Your CPU grinds. You notice the tab is slow. Close it, problem stops. Coinhive ran this model from 2017 to 2019. Ten million users a month were getting their CPUs hijacked by websites they trusted. When Monero crashed 85%, Coinhive shut down and 99% of browser mining stopped overnight. It is not totally dead. Small scripts like CoinImp still pop up. But the gold rush is over.
File-based malware is the persistent kind. Phishing email. Bad download. Malicious ad. Something gets you to click. XMRig drops onto your system, responsible for 43% of all known cryptomining attacks according to Check Point. It sets itself up as a background service, changes your startup scripts so it survives reboots, and hides behind names like "svchost32" or "systemd-helper." Some use rootkits so they do not even show up in Task Manager. You reboot. It comes back. Every time.
Cloud attacks are where the real money is. Or rather, where the real bills are. An attacker steals AWS credentials, spins up p3.16xlarge GPU instances at $24.48 an hour, and mines until the bill arrives. The math is ugly: for every $1 the hacker earns in crypto, the victim pays $53 in cloud charges. USAID lost $500,000 in Azure fees from a single breach in fall 2024. In 2025, worm-like malware started spreading from one Docker container to the next, hitting every exposed API it could find. The attacker never logs in twice. The malware does the work.
| Attack type | How it works | Target | Typical detection time |
|---|---|---|---|
| Browser-based | JavaScript in web pages mines via your browser | Website visitors | Immediate (if tab closes) |
| File-based malware | Phishing or download installs persistent miner | PCs, servers | Days to months |
| Cloud/container | Stolen credentials spin up mining instances | AWS, Azure, GCP, Docker | Weeks (until bill arrives) |
| IoT | Malware infects routers, cameras, smart devices | Home/business IoT | Months to never |
| AI/GPU | Targets ML training clusters and GPU farms | AI infrastructure | Varies |
The cryptojacking threat landscape in 2026
The numbers from SonicWall tell the story clearly.
| Year | Cryptojacking detections | Change |
|---|---|---|
| 2020 | 81.9 million | +28% |
| 2021 | 97.1 million | +19% |
| 2022 | 139.3 million | +43% |
| 2023 | 1.06 billion | +659% |
| 2024 | 332 million | Declined from peak, still elevated |
What caused 2023? Ransomware gangs ran out of easy marks. Law enforcement got aggressive. Victims stopped paying. OFAC sanctions made collecting ransom a legal nightmare. So the same gangs switched to a model that does not require any victim interaction at all. Plant the miner. Collect in silence.
The sectors getting hammered hardest: healthcare up 700% in 2024. Education hit 320x harder than the year before. Governments 89x. India saw a 141% spike in 2025. IoT devices got 97% more attacks because routers and cameras are easy to pop and nobody ever checks their CPU usage.
Cloud is the jackpot. 23% of cloud environments have been hit at some point. The economics are lopsided in a way that rewards the attacker regardless of crypto price. They steal $1 worth of compute and it costs the victim $53 on their AWS bill. A GPU instance burning at $24.48 an hour adds up to six figures before someone checks the dashboard.
Phones are the newest frontier. Mobile cryptojacking grew 60% in 2025. Your phone overheats. Battery dies by noon. You blame the weather or that last iOS update. The miner runs until you wipe the device.
How to detect cryptojacking
Nothing looks broken. Files are fine. Passwords work. But your laptop fan has been screaming for three weeks and you do not know why.
The signs are physical before they are digital. Your CPU sits at 90% while you are reading email. Open Task Manager on Windows or Activity Monitor on Mac. If a process you have never heard of is chewing 70%+ of your CPU, you might have a miner running. XMRig often hides behind names that sound like real system services. "systemd-helper" or "svchost32" in places they should not be.
Heat is the other giveaway. Your laptop burns your thighs. Your phone gets hot in your pocket while you are not using it. Cryptomining hammers hardware nonstop. The temperature never goes down because the miner never stops.
Check your power bill. A cryptojacked PC running 24/7 adds $30-50 a month in electricity. Nobody notices $30 until they look at three months of bills and see the pattern.
Cloud victims find out when the invoice arrives. AWS or Azure charges double or triple. Nobody deployed new instances. Nobody ran extra jobs. But a hacker in Romania spun up GPU machines on your account two weeks ago and they have been mining around the clock. Microsoft documented cases where companies lost over $300,000 before anyone checked the bill.
One website consistently tanks your browser? Could be a mining script. Close the tab, watch your CPU. If it drops back to normal, that site was running code on your machine.
Network monitoring is the professional-grade detection. Miners connect to mining pools to submit hashing results. That creates a pattern: small, regular outbound packets to specific IPs. DNS logs and IDS tools catch this if you know what to look for.

How to prevent and recover from cryptojacking
Most of this is boring IT hygiene. But boring IT hygiene is what stops 90% of cryptojacking.
Patch your software. WannaMine rode EternalBlue. Craft CMS CVE-2025-32432 got exploited for cryptomining within weeks of disclosure. The fix existed. People did not apply it. Do not be those people.
Run antivirus that actually works. Windows Defender, CrowdStrike, Kaspersky, Malwarebytes all catch XMRig and its variants. "Known" variants, anyway. Brand new ones slip through until the signature database catches up. EDR tools give you better odds than basic antivirus.
Install browser extensions that block mining scripts. No Coin, MinerBlock. uBlock Origin catches a lot of them through its ad-blocking filters. This stops browser-based cryptojacking dead.
MFA on every cloud account. The USAID breach cost $500,000 because a test environment admin account had no MFA. One password spray attack. One compromised account. Half a million dollars in Azure bills. Enable MFA. Set billing alerts. Monitor for new instances you did not create.
Do not expose Docker APIs to the internet. I know it sounds obvious. People still do it. Self-spreading mining worms target exposed Docker Engine APIs and jump from container to container. Scan your images before deploying. Watch Kubernetes resource usage.
Already compromised? Kill the process. Find how it got in: check cron jobs, startup scripts, scheduled tasks, container images. Remove the malware. Patch the hole. Rotate every credential. For cloud: terminate unauthorized instances right now and audit who has IAM access to create new ones.