V2Ray VPN: Project V, Protocols, Xray, and Sing-box Forks Tutorial
The V2Ray ecosystem in May 2026 is larger than the singular "V2Ray VPN" of marketing copy suggests. Three actively maintained Go implementations carry the family forward — v2fly/v2ray-core, XTLS/Xray-core, and SagerNet/sing-box — and between them they account for roughly 106,000 GitHub stars. Most articles you read on this subject pick one of them, call it V2Ray, and leave it at that. This one does not. The tool itself is a framework rather than a single program, and the people who connect to it daily for privacy and high-speed internet access in restricted regions usually use one of the three forks below without much thought to the distinction.
What follows is a single-tutorial overview. Where V2Ray came from. The protocols it carries: VMess, VLESS, Trojan, Shadowsocks, and several more. The transports they ride on. The three competing forks and when to pick each. Where to download the software. What clients exist for Windows, Linux, and macOS. And how the V2Ray umbrella has held up under the 2025–2026 wave of state-level censorship pressure.
What V2Ray Is and the Project V Origin Story
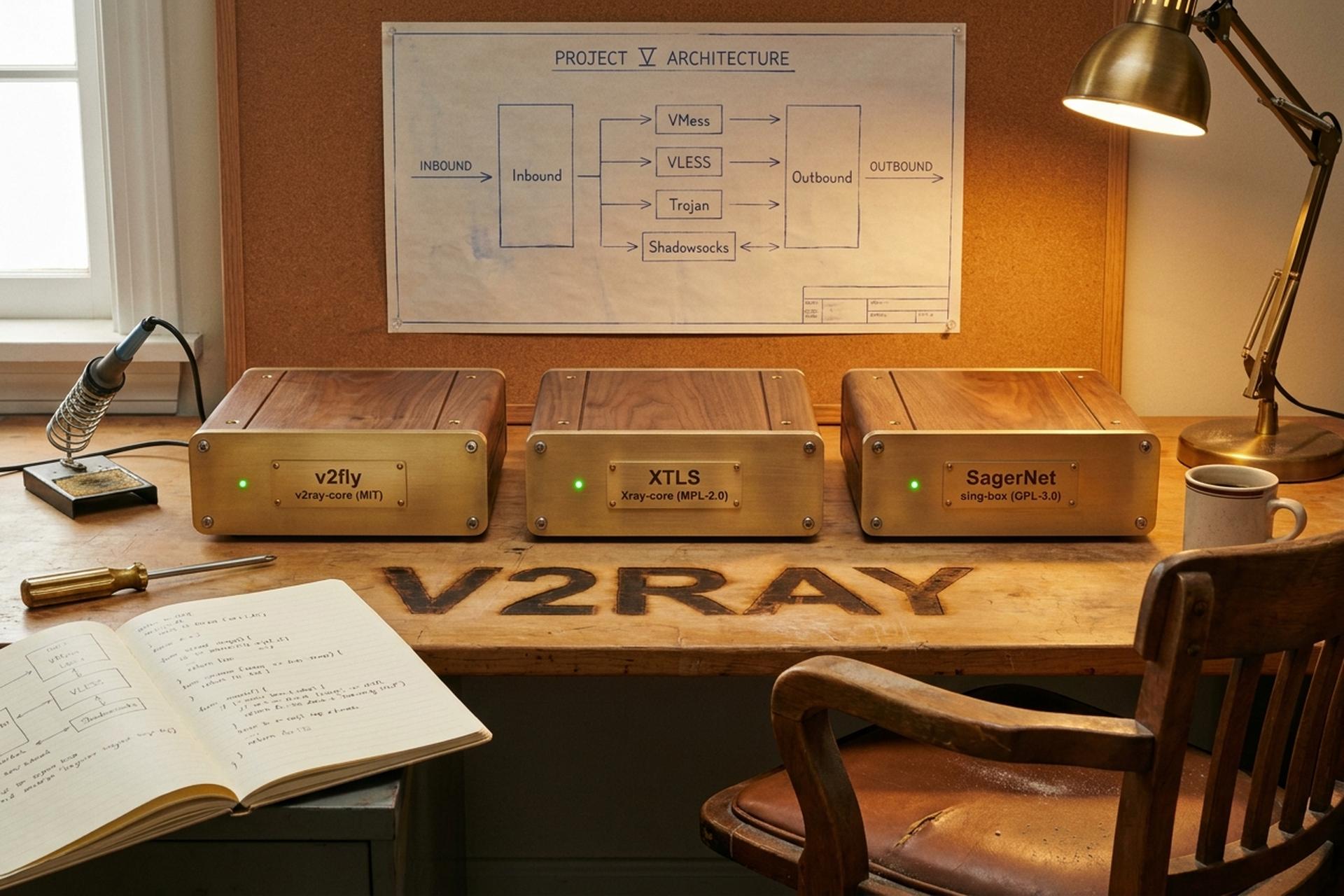
V2Ray is the runtime at the center of Project V — a framework, not a single proxy program, intended from the start to host multiple inbound and outbound protocols behind a common configuration model. Version 0.1 was published on September 18, 2015 under the pseudonym Victoria Raymond, according to the Wikipedia entry on V2Ray and to commit metadata on the original repository.
Raymond stopped responding on every public channel in February 2019. Her GitHub showed sporadic activity until November 2019 and then went quiet. The original v2ray.com infrastructure was abandoned along with the founder's contact addresses, and community maintainers did not have administrative access. In 2020, a community-led fork at github.com/v2fly/v2ray-core became the canonical reference implementation, with new GPG signing keys dated June 2, 2020. When people say "V2Ray" today, this is the codebase they mean.

V2Ray as a Protocol Platform: VMess, VLESS, Trojan, Shadowsocks
The point of V2Ray is that it is not a protocol. It is a platform. A platform that supports multiple protocols. A platform that lets each one ride on whatever transport makes sense. A single V2Ray-core process can run a VMess inbound, a VLESS inbound, a Trojan inbound, and a Shadowsocks inbound at the same time. It can route their traffic through different upstream outbounds. It can apply different routing rules to each.
The protocol roster, as it stands in v2fly/v2ray-core v5.48.0 (released March 26, 2026):
V2Ray VMess is the legacy protocol. It carries its own AEAD encryption and was the platform's flagship for years, providing secure communication between client and server for anticensorship use. PR #170, merged in September 2020 and shipped in v4.28.1, made VMess automatically switch to AEAD authentication whenever the `alterId` parameter equals zero. Older MD5-based authentication was retired across 2021–2022 — now a relic. VMess detection on China's Great Firewall has climbed to roughly 80 percent since September 2025, by community measurement. That is why it has fallen out of fashion for new deployments.
VLESS is the lightweight successor: same UUID-based authentication, no built-in encryption layer, everything delegated to TLS. The VLESS article on this site covers the protocol's internals in depth. For V2Ray's purposes, the important point is that VLESS is what most modern V2Ray-stack users deploy. REALITY on Xray is the common pairing.
Trojan is a sibling design from a different team. It is TLS-only, authenticated by a shared password rather than a UUID, with no addons field. Its minimalism made it strong for years. The GFW upgrade in August 2025 changed that, and Trojan detection now sits around 90 percent.
Shadowsocks is from another lineage altogether: a symmetric AEAD cipher with no TLS facade by default. The 2022 specification known as SIP022 made full replay protection mandatory and retired older ciphers; V2Ray-core has carried it since. Modern Shadowsocks deployments usually pair the cipher with a transport plugin (v2ray-plugin, cloak) to put TLS back on the outside.
SOCKS 4, 4a, and 5 and HTTP are supported as inbound and outbound proxies for local routing. They are useful when you want V2Ray to expose a SOCKS5 endpoint to your browser, or to consume an HTTP proxy upstream.
MTProto is the Telegram-specific protocol. V2Ray-core ships inbound and outbound MTProto handlers, listening on port 443 with a 32-hex-character user secret. It is one of the few non-generic protocols in the platform.
Each protocol is independent of the transport it rides on. That separation is the platform's defining property.
| Protocol | Role | GFW status (May 2026) | Typical use |
|---|---|---|---|
| VMess | Legacy V2Ray flagship | ~80% detection | Backward compatibility |
| VLESS | Lightweight, TLS-delegated | <5% with REALITY | Modern censorship-resistant setups |
| Trojan | TLS-fronting, password auth | ~90% detection | Self-hosted simple proxies |
| Shadowsocks (SIP022) | Symmetric AEAD obfuscation | Mixed (plugin-dependent) | Mobile, flaky networks |
| SOCKS / HTTP | Generic proxy | n/a | Local routing |
| MTProto | Telegram-only | n/a | Telegram clients |
Transports and mux.cool: TCP, WebSocket, gRPC, REALITY
Underneath the protocols sits the transport layer. The transport decides how V2Ray packets travel across the wire. The supported transports in v2fly/v2ray-core are TCP, mKCP (a UDP-based reliable stream), WebSocket, HTTP/2, QUIC, and gRPC. Xray-core adds REALITY (handshake camouflage via TLS impersonation) and the newer XHTTP transport. Each is configurable independently of the protocol. VLESS can ride WebSocket, VMess can ride gRPC, Trojan can ride raw TCP.
Above the transport sits TLS in nearly every real deployment. The default in 2022–2024 was "protocol over WebSocket over TLS over Cloudflare." Cloudflare's CDN provided edge IPs that censors could not block without breaking large parts of the internet. That setup still works in 2026, though Russian and Chinese DPI have learned to recognize TLS-in-TLS patterns when older protocols try to wrap themselves inside an outer TLS tunnel.
mux.cool is V2Ray's multiplexing layer, addressed as "v1.mux.cool" inside configs. It pools multiple proxy sub-connections onto a single underlying TCP socket. The goal is reducing handshake latency, not raising throughput. The practical effect is faster page loads on connection-heavy sites, with no real change in raw bandwidth.
V2Ray vs Xray vs Sing-box: Three Repositories, One Family
Three repositories matter. Each one is a Go program, each one supports VMess/VLESS/Trojan/Shadowsocks, and each one has its own opinions about everything else.
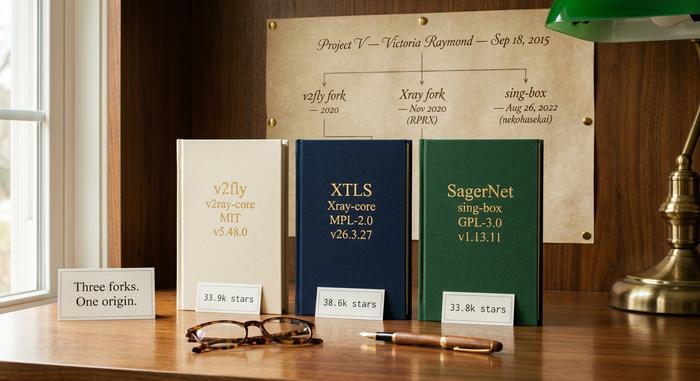
v2fly/v2ray-core is the reference implementation, the spiritual continuation of Project V after Victoria Raymond's disappearance. As of May 2026 it sits at 33.9k stars and 5.0k forks on GitHub, licensed under MIT, with v5.48.0 as the most recent release on March 26, 2026. v2fly's role is canonical: documentation, protocol stewardship, and the geosite and geoip databases that the entire ecosystem consumes.
XTLS/Xray-core is the November 2020 fork by RPRX, who led the VLESS and XTLS effort inside v2fly until licensing disagreements led to a split. The Project X organization was formed, and Xray-core has since become the more actively developed fork: 38.6k stars and 5.4k forks, licensed under MPL-2.0, with v26.3.27 released March 27, 2026. The signature features that live only here are XTLS Vision flow control, REALITY handshake camouflage, and the XHTTP transport.
SagerNet/sing-box is the unifier. nekohasekai started it with v1.0-beta.1 on August 26, 2022, and the project has grown into the cleanest cross-protocol Go binary in the space: 33.8k stars, 4.0k forks, GPL-3.0, v1.13.11 released April 23, 2026. Sing-box speaks every V2Ray protocol plus the newer generation: Hysteria, TUIC, Naive, and REALITY. For new deployments where the operator wants to mix and match, sing-box is usually the easier starting point.
| Implementation | Stars | License | Latest | Signature feature |
|---|---|---|---|---|
| v2fly/v2ray-core | 33.9k | MIT | v5.48.0 (Mar 2026) | Reference implementation, geosite/geoip |
| XTLS/Xray-core | 38.6k | MPL-2.0 | v26.3.27 (Mar 2026) | XTLS Vision, REALITY, XHTTP |
| SagerNet/sing-box | 33.8k | GPL-3.0 | v1.13.11 (Apr 2026) | Multi-protocol unified binary, Hysteria/TUIC |
Which one to pick depends on the use case. For maximum protocol fidelity to upstream V2Ray, run v2fly. For censorship resistance against active state DPI, run Xray with REALITY. For a single binary that can speak almost everything and exposes modern tooling, run sing-box.
V2Ray Routing: geosite, geoip, and Smart Connections
V2Ray's customizable routing engine is the feature that quietly justifies the rest of the configuration complexity. The engine evaluates rules from top to bottom, matching on domain category, IP CIDR, port, network type, source IP, and inbound tag. The data behind it lives in two protobuf-encoded binaries. `geosite.dat` holds domain categories (Chinese sites, Iranian sites, ad networks, streaming services). `geoip.dat` holds IP-to-country mappings. The v2fly/geoip repository rebuilds both automatically on a monthly cadence, drawing from public lists.
The typical real-world configuration uses split tunneling: domestic sites bypass the proxy and route through the local connection, while everything else goes through the outbound. Operators in China commonly write rules that match the `geosite:cn` and `geoip:cn` categories to direct domestic traffic locally, leaving the proxy for foreign destinations. The same pattern reversed works for users abroad who want their banking traffic to keep its real geography.
How to Download V2Ray-core: GitHub Releases, Packages, Docker
There are three reasonable ways to install V2Ray-core, depending on the host.
GitHub releases. The github.com/v2fly/v2ray-core/releases page carries signed tarballs for every supported platform: Linux on amd64 and arm64, Windows, macOS, Android (ARMv7 and ARM64), FreeBSD, and Dragonfly. Each release ships SHA256 sums and a GPG signature; the keys are documented in the repository's README.
Distribution packages. The official `fhs-install-v2ray.sh` script (hosted under v2fly/fhs-install-v2ray) installs V2Ray-core into the Filesystem Hierarchy Standard layout, dropping `/usr/local/bin/v2ray` for the binary, `/usr/local/etc/v2ray` for configs, and a systemd unit for service management. On Arch-family Linux there is an AUR package, and on Homebrew community formulae carry the same binary. No first-party Snap or AppImage exists, since V2Ray is daemon-class software designed to run under a service manager rather than a sandbox.
Docker. The v2fly Docker repository (`v2fly/v2fly-core`) publishes images for every release, useful when V2Ray-core needs to run alongside a stack of containers managed by Compose or Kubernetes.
Whichever path the operator picks, the next step is the same: write a JSON configuration, point V2Ray at it, and watch the daemon start.
V2Ray Clients: v2rayN Install on Windows, Linux, Mac OS
On the client side the ecosystem is fragmented but mostly reliable.
Windows. v2rayN is the dominant choice: a system-tray Windows GUI that imports VMess and VLESS subscription URIs, manages multiple servers, exposes traffic statistics, and runs the V2Ray-core binary in the background. Install is a download-and-unzip from the v2rayN GitHub releases page. The GUI defaults to Chinese on first launch and is well-known for that quirk.
Android. v2rayNG is the rough Android equivalent: same import format, same workflow, available on F-Droid and the Play Store. NekoBox is the sing-box-flavored alternative, with a wider protocol set including Hysteria and TUIC. Hiddify is the cross-platform option that also runs on Android.
Mac OS. The legacy Mac clients V2RayX and V2RayU have not seen serious updates in years. Hiddify is the modern recommendation on macOS, with Sing-box for Apple available as a cleaner native option. Installation is a standard `.dmg` from the project's releases page.
Linux. Most Linux users run V2Ray-core directly via systemd and route their browser through a local SOCKS5 inbound. For desktop GUI, Nekoray and Hiddify both run on Linux and produce the same UX as their Windows counterparts.
iOS. Streisand is the free option; Shadowrocket and V2Box are the paid ones. All three import vless:// and vmess:// URIs and call into Apple's Network Extension framework to tunnel traffic.
V2Ray and the 2025–2026 Censorship Bypass Pressure
The pressure on V2Ray-stack protocols intensified through 2025 and into 2026. A May 2026 InstaTunnel analysis put GFW detection at roughly 90 percent for Trojan after the August 2025 firewall upgrade and 80 percent for VMess after the September follow-up. Russia's Roskomnadzor blocked 469 VPN services by February 2026, up from 439 in January, and began active interference with VLESS+TLS handshakes at the TSPU layer in late 2025.
The practical migration path, visible in community panels and operator chats, has been away from "naked" VMess and Trojan deployments and toward camouflaged stacks: VLESS+REALITY on Xray, or sing-box configurations that mix Hysteria and TUIC for UDP-friendly routes. The V2Ray umbrella has held up not because the framework itself is invisible (it is not), but because the protocols inside it can be swapped out faster than censors can train new detection models. That trade-off is what the platform was designed to protect.