Shodan: The Hacker’s Search Engine in 2026 Explained

Shodan is the search engine that taught the security industry just how much of the physical world plugs straight into the open internet, and how often that exposure happens through a default password rather than a movie-style zero-day. The most cited case of the recent cycle is not a Hollywood breach. It is the Aliquippa, Pennsylvania water-authority controller compromised on 25 November 2023 by typing "1111" into a Unitronics PLC on port 20256. CISA's advisory AA23-335A named at least 75 compromised PLCs across multiple US sectors after the same group, CyberAv3ngers, swept on. Shodan is also, separately, the name of an AI antagonist from a 1994 video game called System Shock, which is where the search engine took its name. This guide covers what the search engine actually does in 2026, what it exposes, and what is and is not legal to do once you find a device on it.
What Shodan is, in one paragraph
Shodan indexes devices connected to the internet, not web pages. That is the cleanest one-sentence answer, and the part most people miss until they actually run a search. The crawler hits a long list of common service ports across the IPv4 space and reads back whatever banner each one happens to return. Version strings, certificates, HTTP headers, sometimes a screenshot of a login screen. That metadata is what becomes searchable. John Matherly first sketched the idea in 2003, but the public service did not go live until 2009. The result of a query is not a webpage. It is an IP with fields attached. Google ranks pages; Shodan ranks endpoints.
Where the name comes from: SHODAN from System Shock
The all-caps SHODAN is an acronym from a 1994 cyberpunk-horror game: Sentient Hyper-Optimized Data Access Network. In the fiction, she starts out as the artificial intelligence running a deep-space research and mining station, voiced by Terri Brosius with that deliberate stutter and flat affect everyone who played the game still remembers. Her ethical constraints are stripped away early in the backstory, and by System Shock 2 in 1999 she has attached her consciousness to a jettisoned module and returned with a grudge. Critics rank her consistently among gaming's strongest villains, and most observers credit her as the design ancestor of GLaDOS from Portal. System Shock 3 was announced back in 2017 and has rolled through several troubled hand-offs since, with Nightdive Studios (the team that already remastered the original) the most recent steward of the IP. Ken Levine, who wrote System Shock 2, later went on to make BioShock. Matherly borrowed the name as a knowing nod, because a cybernetic entity that sees everything is roughly what the search engine grew up to be.
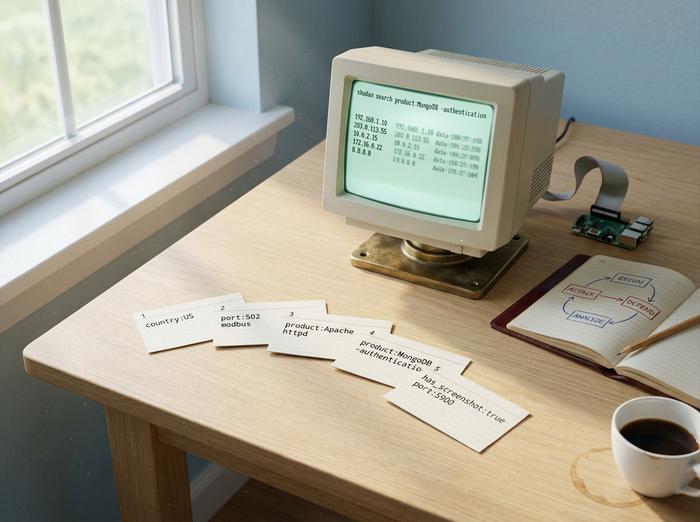
How to use Shodan: search syntax that actually works
Shodan's web interface accepts a search query that is mostly free text plus key:value filters. The filters are where it stops being a curiosity and starts being a tool.
| Filter | What it does | Example |
|---|---|---|
| `country:` | Restrict to a country code | `apache country:US` |
| `port:` | Restrict to a service port | `port:22` |
| `org:` | Restrict to an organization | `org:"Apple"` |
| `product:` | Filter on detected product | `product:"Apache httpd"` |
| `version:` | Filter on version string | `version:"2.4"` |
| `http.title:` | Filter on HTTP page title | `http.title:"login"` |
| `has_screenshot:true` | Only results with a captured screenshot | `port:5900 has_screenshot:true` |
| `ssl.cert.expired:true` | TLS certificates past their validity | `ssl.cert.expired:true port:443` |
The plan tiers shape what you can do. A free account returns the first 10 results per query. Registered accounts get 50. The Membership tier is a one-time payment that has drifted between $49 and $69 depending on the month and on which Black Friday Matherly is running. Above that sit Small Business, Corporate, and Enterprise plans for commercial users, with monthly query credits and access to features like Shodan Monitor and Shodan Trends. There is also a free InternetDB API that returns light metadata for a given IP without a paid account, designed for developers integrating exposure checks into security workflows.
The industrial filters are where Shodan earned its reputation. `port:502` finds Modbus controllers. `port:102 product:Siemens` finds S7 PLCs. `port:47808` finds BACnet building-automation systems. Power-user queries can pull a lot of weight in about five minutes: `product:MongoDB -authentication` lists unauthenticated MongoDB instances, `"authentication disabled" "RFB 003.008"` lists open VNC sessions, `http.title:"OctoPrint" -title:"Login"` returns unprotected 3D printers, and `mikrotik streetlight` finds city traffic-light controllers still running default RouterOS.
The CLI is the workhorse for any programmer or developer running the queries day to day. Install with `pip install shodan`, set your key once with `shodan init `, then `shodan search`, `shodan count`, and `shodan host` cover most ad-hoc work. The Python library exposes the same Shodan platform surface programmatically. Maltego, Metasploit, and Recon-ng all integrate Shodan for chaining queries into a wider workflow, and cyber market intelligence tools layer on top for SOC dashboards. The internet of things, as a security category, is largely defined by what these queries surface.
Shodan for cybersecurity: red team and blue team
Three audiences run Shodan queries every day, for very different reasons: red teams, blue teams, and bug-bounty hunters.
For red teams and penetration testers, Shodan handles the reconnaissance step before any active scanning starts. The workflow is to drop the target organization into an `org:""` filter and read back the external attack surface as the world already sees it. That step stays fully passive, which is the point, because Shodan already did the scanning and the operator is just reading cached results. Bug-bounty research on Bugcrowd and HackerOne runs the same pattern, since misconfigured in-scope assets are often the fastest path to a payout.
For blue teams, Shodan flips into something close to a defensive product. Shodan Monitor watches your registered IP ranges continuously and pings you when a new service exposes itself or when an existing service changes its banner. The use case is attack-surface management without standing up a full commercial ASM platform. CISA advisories regularly cite Shodan-discoverable exposures as the dwell-time problem they were built to flag, frequently pairing the banner with a CVE so a defender can pivot to a real-time exploit-availability check.
For comparison context, Shodan is not the only engine. Censys, which spun out of the University of Michigan, scans all 65,535 ports against Shodan's 1,237. It detects new services in about 12 hours, against Shodan's 76. ZoomEye, based in China, sits in between with around 3,828 ports. Despite that coverage gap, Shodan still owns the developer tools and the free-tier ergonomics. It is the engine practitioners actually open first.
A short word on legality here, since this is where junior pentest engineers get themselves in trouble. Running a Shodan query is legal in the US, the EU, and the UK. So is reading the banner that comes back. The Computer Fraud and Abuse Act in the US starts to bite the moment somebody logs into or interacts with the device behind that banner without permission. The Auernheimer reversal in the Third Circuit in 2014, and the hiQ Labs v. LinkedIn decision in the Ninth Circuit in 2022, have shifted the conversation toward "access without authorization" rather than scanning. That gives security professionals more room for passive recon. It does not create a license to log in.
What Shodan exposes: a real-world horror tour
Only verified incidents here. The cleanest recent example is the Aliquippa case. On 25 November 2023 attackers reached a Unitronics Vision-series PLC at the Municipal Water Authority of Aliquippa, Pennsylvania, on TCP port 20256, and authenticated with the out-of-box password "1111." The persona claiming credit was CyberAv3ngers, which CISA has tied to the IRGC. The joint advisory AA23-335A that followed named at least 75 compromised US PLCs spanning water, wastewater, food and beverage, and manufacturing. There was no zero-day involved, no real skill required, just a controller with the out-of-box configuration sitting in plain sight on the open internet.
Behind every Aliquippa-style headline sits a much larger, quieter backdrop of unauthenticated databases. Counts have varied between 35,000 and 194,000 across MongoDB studies and snapshots, with Elasticsearch and Redis sitting in similar magnitudes. The recurring ransom marker (instances renamed to `READ_ME_TO_RECOVER_YOUR_DATA`) keeps showing up from 2017 forward, year after year, without obvious end. MQTT brokers running Mosquitto with no authentication have repeatedly been counted above 80,000, which is most of the IoT messaging substrate operating in the open.
Industroyer / CrashOverride took down a Ukrainian power station in 2016. Not strictly a Shodan story, but the same discovery pattern: find exposed industrial control systems by service banner, then attack the protocol they speak. Mirai, the 2016 botnet that briefly knocked Dyn offline, ran its own scanning rather than relying on Shodan, although the technique was identical: find IoT devices with default credentials on Telnet and SSH, add them to the herd. The followup point matters: Mirai's source code went public in October 2016, and variants have continued to recruit new devices for nearly a decade since, because the underlying weakness (manufacturers shipping with default passwords) was never structurally addressed.
Exposed industrial cameras are probably the most cinematic Shodan result and certainly the most consistent over time. Pair the `port:554` filter with `has_screenshot:true` and you get back hundreds of thousands of webcams and security camera feeds, many still on the original installer credentials. The screenshots appear inside the search results themselves. That is what gives Shodan its uncomfortable reputation with non-technical readers who land on the homepage by accident, and it is also what gets the engine into journalism. Power plants, traffic lights, and routers with default credentials surface in the same way through more boring filters: `port:502` for ICS, `mikrotik streetlight` for the city traffic networks, `port:21` for anonymous FTP. The fix at the device level has not changed since 2013, which is exactly the problem: change the default password, put the camera or PLC behind a VPN or reverse proxy, do not give the box a public IP. Every successful hack of an exposed device traces back to that same omission.
One commonly miscited example deserves correction. Verkada is not a Shodan story. The March 2021 breach that exposed 150,000 customer cameras started at a misconfigured customer-support server with leaked super-admin credentials, not through internet-exposed cameras. The FTC's $2.95 million penalty in August 2024 was technically over CAN-SPAM violations bundled into a 20-year audit consent order. Worth flagging because the case still turns up in nearly every Shodan explainer where it has no business being.
Is Shodan legal? And the ethics of scanning
In short, yes. Running a Shodan query is legal. Reading the banner Shodan returns is legal. The grey area starts when somebody acts on the result. If you find an exposed device that is not yours, the rule is the same as the rule for an unlocked front door: looking is fine, walking in is not. Logging in to a device you do not own without authorization is what the Computer Fraud and Abuse Act actually polices in the US, and CFAA decisions over the past decade have narrowed toward "authorization" rather than "scanning." The UK Computer Misuse Act and the EU's NIS2 framework reach similar conclusions through different language.
The practical ethical rule for security professionals is to assume any device Shodan shows you still belongs to its owner. Use a coordinated vulnerability disclosure channel, your country's CSIRT, or a published security.txt to report the exposure. Bug bounty researchers should never test beyond banner reading on out-of-scope assets, and reputable platforms like HackerOne and Bugcrowd will take you off the program for doing so. The line is not technical. It is intent and consent.
One nuance worth flagging: even passive lookups have audit trails on the Shodan side, and enterprise legal teams sometimes object to employees querying competitor IP ranges even where the query itself is legal. The conservative move in a corporate setting is to query only your own assets and your authorized targets, and to keep a record of why each query was run.

Shodan vs Censys vs ZoomEye for developers
| Engine | Ports scanned | Avg new-service detection | Free tier | Origin |
|---|---|---|---|---|
| Shodan | ~1,237 | ~76 hours | 10 results unauthenticated, 50 registered | John Matherly, 2009 |
| Censys | 65,535 (full) | ~12 hours | Limited query credits with academic access | University of Michigan |
| ZoomEye | ~3,828 | Mid-range | Free with registration | Knownsec, China |
Shodan wins on developer experience and library quality. Censys wins on coverage and certificate analytics. ZoomEye matters for some Asia-Pacific protocol coverage. Most production security workflows query at least two of the three through their CLI.
For all the worry Shodan attracts, what it really does is hold a mirror up to the public internet — the exposures it surfaces are not its fault, they are configuration choices made on the device side. The fix in 2026 is the same as it was in 2009: change default passwords, expose less, monitor your own footprint first, and assume that anyone who wants to find your devices already has.