Blockchain Security in 2026 : Threats, Vulnerabilities, Defences

$3.4 billion stolen in 2025. Most of it not from broken cryptography. The blockchain network and its ledger technology rarely fail at the protocol level. The systems built around them — wallets, signing UIs, developer machines, supply chains — fail constantly. Chainalysis traces roughly $2 billion of last year's losses to DPRK-linked actors, and the February 2025 Bybit heist alone accounted for $1.5 billion. One incident. Two-thirds of the year. The pattern is consistent: cryptography and consensus hold; key management, signing flows, smart-contract logic, and human operators do not.
This guide walks the 2026 landscape. How blockchain security actually works. What broke in the major incidents of 2022 to 2025. What defensive teams now do across smart contracts, key custody, network-layer threats, audits, regulation, and the research frontier. The threats and vulnerabilities targeting blockchain systems today are the practical baseline for any conversation about security in blockchain.
What blockchain security is in 2026
Blockchain security refers to the practical study of keeping a distributed ledger tamper-evident, its consensus mechanism honest, and the assets it represents under their owners' control. The term covers everything from cryptography and information security to operational best practice across the blockchain ecosystem. NIST Internal Report 8202 has been the foundational US government framing since 2018, organising the field around three pillars: cryptographic primitives such as hash functions and asymmetric keys, consensus protocols, and the permissioning model of a chain. That framing still holds. Consensus security boils down to the economic and computational cost of rewriting history. In Proof of Work, an attacker controlling more than 50% of hash power can reorganise the chain or double-spend. In Proof of Stake, the analogous threat is a one-third or two-thirds stake attack on Casper FFG finality. Bitcoin uses probabilistic finality (six confirmations as a heuristic). Ethereum reaches economic finality roughly 12.8 minutes after a block.
Types of blockchain and how each affects security
Different types of blockchain run different security models. The trust assumptions baked into each are the security model itself. Public blockchain networks like Bitcoin, Ethereum, Solana and Sui treat any node in the distributed network as a potential validator. Cryptocurrency rewards keep every miner and staker honest. The number of nodes is open-ended. The security of the blockchain is paid for in mining power or staked capital. NISTIR 8202 puts it directly. Permissionless consensus promotes non-malicious behaviour by rewarding publishers of protocol-conforming blocks with a native cryptocurrency. Censorship resistance and global access — paid for in attack surface. An open node set means an open Sybil surface, and economic security tracks the price of the underlying token.
A permissioned blockchain or consortium chain (Hyperledger Fabric, R3 Corda, ConsenSys Quorum) replaces economic incentives with vetted identity. Validator sets are small, BFT-style protocols give immediate finality, and access controls gate who can read, write, or validate transactions. The trade-off runs the other way: a small consortium of blockchain participants is faster and cheaper but introduces a single point of failure if that consortium colludes or is compromised. A hybrid blockchain combines elements of both, with public settlement and private permissioning.
Most enterprise distributed ledger technologies and blockchain technologies in 2026 sit somewhere on this spectrum. Private blockchains are common in financial services for inter-branch settlement, while public blockchains carry retail and DeFi flows. The right question is not which type of blockchain is more secure in the abstract; it is which threat model the architecture is built to defend against. A bank running a private blockchain in the financial services industry does not need 51%-attack resistance; it needs role-based access controls, audit logging, and disaster recovery to ensure availability of data. A public DeFi protocol needs the opposite priorities, and the security of blockchain settlement matters more than uptime SLAs.
Major blockchain attacks and incidents 2022-2026
The incident table tells the story of how blockchain attacks have evolved. Bridges and validator-key compromises dominated 2022. Centralised exchanges and signing-flow attacks dominated 2025.
| Incident | Date | Loss | Attack vector |
|---|---|---|---|
| Ronin Bridge | Mar 2022 | $625M | Validator key compromise (5 of 9) |
| Wormhole | Feb 2022 | $325M | Signature verification flaw |
| Nomad Bridge | Aug 2022 | $190M | Faulty Replica initialisation |
| DMM Bitcoin | May 2024 | $305M | Private key compromise (TraderTraitor / Lazarus) |
| WazirX | Jul 2024 | $235M | Multisig wallet manipulation |
| Bybit | Feb 2025 | $1.5B | Safe{Wallet} UI injection during cold-wallet signing |
| Cetus DEX (Sui) | May 2025 | $223M | `checked_shlw` overflow in u256 fixed-point math |
The Cetus exploit is illustrative of how primitive math errors persist in production. SlowMist's post-mortem describes how the attacker selected parameters precisely to abuse a flaw in the `checked_shlw` shift operation, draining liquidity worth roughly $223 million at the cost of one token. Chainalysis 2025 mid-year reporting put losses at $2.17 billion by Q2, with centralised-service compromises responsible for 88% of Q1 totals. Two-thirds of 2025 dollar losses concentrate in a single incident; DPRK actors have moved upstream from contracts to operators; the most expensive failures of the past two years have not been zero-days in Solidity — but human-and-UI compromises around legitimate signers.
The Bybit hack: a 2025 blockchain security case
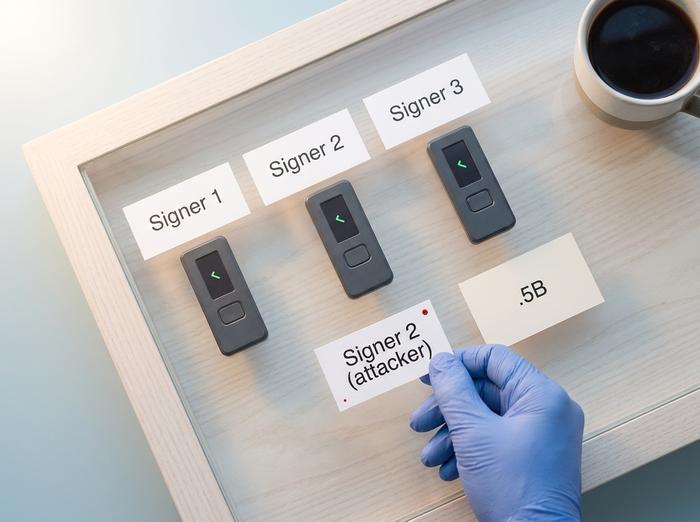
The February 2025 Bybit heist is the canonical case study of where blockchain security fails in 2026. NCC Group's post-mortem details how attackers compromised a developer machine inside Safe{Wallet}, used that access to inject malicious JavaScript into the multisig signing UI, and rerouted approvals while internal signers saw a legitimate destination on screen. The Bybit cold wallet was a 3-of-N Safe, a setup most institutional security teams would have approved on paper. The signers signed what they thought was a routine transfer — the chain executed the attacker's transaction instead.
The lessons run deeper than "improve your operations." First, hardware wallets do not protect against blind signing if the user authorises a malicious payload. Second, multisig is necessary but not sufficient when the UI itself is the trust boundary. Third, the entire chain of trust now extends through the signer's display software, the underlying frontend, the developer machines that build that frontend, and the package supply chain. NCC Group's recommended mitigations include pre-signing transaction simulation, raw-data verification on a separate device, mandatory delays on large withdrawals, and signer hardware that decodes calldata for human review. Trail of Bits' June 2025 retrospective reinforces the point: across the major losses of the year, the most common root cause was not smart-contract bugs but private-key compromises and the operational failures around them.
Smart-contract risks: OWASP Top 10
The OWASP Smart Contract Top 10 (2025 release) ranks each vulnerability by attributable losses in the prior year. Access Control failures dominate at $953 million; Logic Errors come second at $63.8 million; Reentrancy and Flash-Loan Attacks round out the top four.
| Rank | Category | 2024 losses |
|---|---|---|
| 1 | Access Control | $953.2M |
| 2 | Logic Errors | $63.8M |
| 3 | Reentrancy | $35.7M |
| 4 | Flash-Loan Attacks | $33.8M |
| 5 | Lack of Input Validation | $14.6M |
| 6 | Price Oracle Manipulation | $8.8M |
| 7 | Unchecked External Calls | $0.55M |
Trail of Bits' Slither for static analysis, Echidna for property fuzzing, and Manticore for symbolic execution remain the practical baseline; the SWC Registry catalogues the underlying weakness classes. The 2025 OWASP refresh split Price Oracle Manipulation and Flash-Loan Attacks into distinct categories from Logic Errors and retired Timestamp Dependence and Gas Limit Issues into the Logic Errors bucket.
Cryptography and the quantum horizon
Public chains rely on a small set of cryptographic primitives. SHA-256 for Bitcoin. Keccak-256 for Ethereum. BLAKE2 and BLAKE3 for newer chains. Signatures: ECDSA over secp256k1 (Bitcoin, Ethereum), Ed25519 (Solana, Sui, Cosmos), and BLS12-381 for Ethereum consensus aggregation. The threat landscape shifted in August 2024. NIST finalised three post-quantum standards: FIPS 203 ML-KEM, FIPS 204 ML-DSA, FIPS 205 SLH-DSA. FIPS 206 (FN-DSA) is in draft.
Vitalik Buterin's 2024 Ethereum Research post laid out a different defence. Hard-fork to the last block before a visible quantum-theft event. Freeze ECDSA-based externally-owned accounts. Let holders prove ownership via a STARK over their BIP-32 seed. He puts the chance of cryptographically relevant quantum computers arriving before 2030 at about 20%. His February 2026 roadmap targets hash-based validator signatures and EIP-8141 wallet flexibility. Quantum-resistant signature aggregation needs production-ready tooling well before the threat materialises. Not after.
Key management and crypto security architecture
Most 2024-2025 losses originated in custody. The architectural ladder of crypto security has barely moved in 2026. Hot wallets are fast. They are also broadly attacked. Cold wallets are strong on paper. The Bybit heist proved the signing UI itself is now the attack surface. Multi-sig (Gnosis Safe) dominates EVM custody. MPC threshold-signature services from Fireblocks, Coinbase Custody and Copper remove single-key risk. They do not remove operator collusion or signing-flow tampering. Hardware security modules at FIPS 140-2 and 140-3 levels remain the institutional standard for hot-wallet rotation. Account Abstraction under ERC-4337 brings session keys, social recovery and seedless onboarding. It also widens the validation and execution surface.
Mitigations have caught up only partially. Pre-signing transaction simulation. Raw-data verification on a separate device. Mandatory delays on large withdrawals. Signer hardware that decodes calldata. The principle has not changed across the ladder: a private key never leaves a controlled boundary, and every signing event is reviewed against an independent source of truth before it touches the chain.

Network-layer threats: Sybil attacks and MEV
A Sybil attack is the cheap creation of pseudonymous identities to bias a peer-to-peer system; permissionless networks are designed against it but never fully immune. Eclipse attacks build on Sybil: Heilman, Kendler, Zohar, and Goldberg's 2015 USENIX paper showed Bitcoin nodes could be isolated by monopolising peer slots, and 2025 work demonstrated end-to-end eclipse on Ethereum execution-layer nodes by poisoning the discovery table. BGP hijacks (Erebus-style) operate at the autonomous-system level and reroute traffic before it reaches the application. The most economically active layer is now MEV: ESMA's July 2025 risk analysis and Flashbots data show roughly 90% of Ethereum blocks are built via MEV-Boost, with sandwich extraction down to about $2.5 million per month by October 2025 from a peak near $10 million per month in late 2024.
Audits and formal verification
Audit cost ranges in 2026 are predictable. $10k-$50k for small ERC-20 or ERC-721 reviews. $80k-$250k for typical DeFi protocols. $300k-$500k+ for novel rollups, ZK circuits, and L1 components. The top firms list in 2026: Trail of Bits, OpenZeppelin, ConsenSys Diligence, CertiK, Halborn, Spearbit and Cantina, Zellic, Sigma Prime, Veridise (ZK specialist), Certora (formal verification), and Runtime Verification. Formal verification has crossed from research into production. Certora Prover and Veridise's Picus and Vanguard target Solidity, Vyper, Move, and ZK-circuit DSLs. Veridise's published data is sharper than the headline. 55% of its ZK audits surface a critical issue. Regular DeFi audits sit at 27.5%. Under-constrained circuits carry roughly a 90% chance of critical-or-high findings.
Regulation: MiCA, OCC, and CISA
EU MiCA Title V applies from 30 December 2024. National grandfathering runs until 1 July 2026 at maximum. CASPs (crypto-asset service providers) take on hard obligations: custody segregation, IT security, governance, incident reporting on tight clocks. Capital floors are concrete. €50k for advice. €125k for custody and exchange. €150k for trading platforms.
The US picture is messier. OCC Interpretive Letters 1170, 1174, and 1183 let national banks custody crypto, run stablecoin payment rails, and use distributed-ledger networks under safety-and-soundness controls. CISA, FBI and Treasury named Lazarus, APT38, BlueNoroff and Stardust Chollima as TraderTraitor in joint advisory AA22-108A. The FBI February 2025 PSA pinned the Bybit theft on the same cluster. ISO/TC 307 covers the international standardisation track for governance and security.
Security best practices and defensive frameworks
The 2026 defensive playbook borrows from mainstream cybersecurity and combines secure development lifecycle work with runtime detection. The security frameworks and security controls that work at scale share three traits: continuous monitoring, automated invariants, and rehearsed incident response. Real coverage in this context means addressing both smart contract vulnerabilities and the wider blockchain security risks around operators, data security, and the small number of nodes that act as choke points. Slither, Mythril, Aderyn, and Echidna run in CI pipelines; Certora rules express invariants for formal-verification gates; Foundry property fuzzing handles the gap between unit tests and audits. Bug bounties pay real money: Immunefi has paid out over $115 million across 3,000+ reports, with the largest single payout at $10 million (Wormhole) and 77.5% of payouts being smart-contract findings.
Runtime detection is the newer layer. Forta Firewall screened 271.8 million transactions by July 2025 using its FORTRESS neural network for sub-block scoring, with Hypernative as the leading commercial peer; both produce real-time risk scores that can pause a contract before a malicious transaction confirms. Incident response now includes pre-coordinated war rooms, on-chain tracing through Chainalysis Reactor or TRM Labs, exchange freeze contacts, and white-hat counter-exploit rehearsals. The last of those recovered roughly $162 million of the Cetus losses, a reminder that security best practices include the steps you take after the alert fires, not only the ones that try to prevent it.
Cutting-edge research and open problems
Three research fronts are reshaping blockchain security beyond 2026, and each is opening new security risks. Zero-knowledge proof systems are the most fragile link. About 96% of documented bugs in SNARK-based ZK systems trace to under-constrained circuits, per IACR ePrint 2024/514. Tooling like Picus, Coda and Circomspect is now load-bearing for any protocol shipping ZK in production. MEV-resistance has moved from theory to deployment. Encrypted mempools (Shutter), threshold-encrypted ordering, and intent-based architectures (UniswapX, CoW Swap, Across, Flashbots' SUAVE) replace block-builder discretion with cryptographic constraints. Each adds attack surface around solver collusion and proof systems. Account Abstraction under ERC-4337 widens the validation and execution surface — paymasters, bundlers, social-recovery guardians — in exchange for killing seed-phrase risk for most users.
How to think about blockchain security today
Two camps. Protocol people, and operator people. The split matters because the threats split the same way. Build a chain, or help decentralize one, and the work is consensus design, client diversity, security audits, cryptographic agility. Run on someone else's chain and the work is key custody, signing-flow integrity, audited contracts, runtime detection. The 2024 and 2025 losses were almost all operator-side. About $3.4B of them. Pick security measures that match your role, not the headline of the day.