Flipper Zero: the pocket-sized multi-tool that hacks everything (and why governments hate it)

I watched a 19-year-old on TikTok change the channel on a bar TV using an orange plastic gadget while the bartender looked around for the remote. Twelve million views on that clip. Then I watched Canada's government announce they wanted to ban the gadget because it was supposedly being used to steal cars. Then I watched Amazon pull it off their store. Then I watched the company behind it report $80 million in 2023 revenue anyway.
Welcome to the Flipper Zero saga. $169 for a pocket-sized hacking multi-tool for pentesters and geeks. The most controversial consumer electronics product since someone figured out you could jailbreak an iPhone. Politicians hate it because they think it steals cars (it does not). TikTok loves it because you can do dumb pranks with infrared signals. And buried under all the noise is a genuinely useful open source tool that changed how security professionals do their job.
Here is what it actually does, what it absolutely cannot do no matter what social media tells you, and why entire governments lost their minds over a device with a cartoon dolphin on the screen.
What Flipper Zero is: hardware for geeks who like breaking things
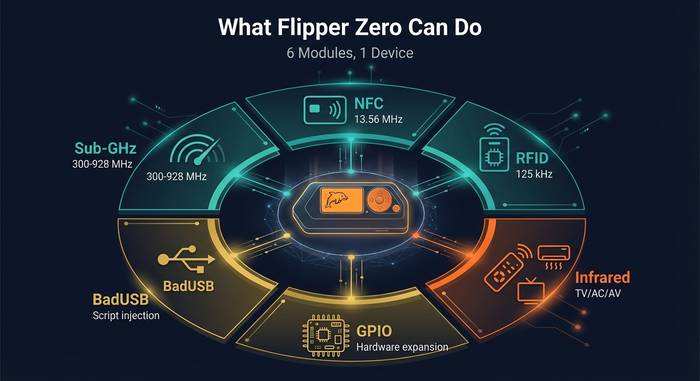
Strip away the controversy and the Flipper Zero is a portable multi-tool device for wireless protocols and access control systems. Swiss Army knife for radio signals, basically. Reads RFID badges. Clones NFC cards. Captures and replays Sub-GHz remote signals. Fires infrared codes at every TV in range. All from a gadget the size of a fat candy bar with a pixel-art dolphin living on its lcd screen.
Alex Kulagin and Pavel Zhovner launched the Kickstarter in 2020. Raised $4.8 million, which was roughly 10x their goal. Flipper Devices Inc. shipped the first units in 2022. By 2025 they had moved over one million of them.
Here is what you get for $169:
| Component | Specification |
|---|---|
| Processor | STM32WB55 (dual-core ARM) |
| RAM / Flash | 256 KB / 1 MB |
| Display | 128x64 pixel monochrome lcd |
| Battery | 2,000 mAh LiPo |
| Sub-GHz radio | CC1101 (300-928 MHz) |
| NFC | ST25R3916 (13.56 MHz) |
| RFID | 125 kHz reader/writer |
| Infrared | Transmitter + receiver |
| Connectivity | Bluetooth LE, USB-C, gpio pins |
| Storage | microsd card slot |
| Size / Weight | 100x40x25 mm / 104 grams |
| OS | FreeRTOS (open source) |
The directional pad and small screen make it look like a 90s Tamagotchi. That is intentional. The dolphin mascot evolves as you use the device. The more you hack, the happier your dolphin gets. Silly? Yes. Brilliant marketing for the hacker community? Absolutely.
What Flipper Zero can actually do
Let me walk through each module because the capabilities are genuinely impressive for a $169 gadget.
Sub-GHz radio. The CC1101 antenna picks up and transmits on frequencies between 300 and 928 MHz. This covers garage door openers, weather stations, remote-controlled gates, wireless doorbells, car key fobs using fixed codes, and dozens of other radio protocols. You point the Flipper at a remote, capture the signal, save it, and replay it later. I have seen people use this to control gates in their apartment complex after losing the original remote.
NFC at 13.56 MHz. The flipper zero has a built-in NFC module that reads contactless cards: transit passes, hotel keys, office badges, payment cards (partially). It can emulate some of these cards, acting as a clone. The nfc module works with MIFARE Classic, NTAG, and several other tag types.
125 kHz RFID. Older access badges, key fobs, and building entry cards often use 125 kHz. The Flipper reads, stores, and emulates these. Walk up to your office badge reader, tap your Flipper instead of your card, and the door opens. Useful when you forget your badge. Also useful for security testing.
Infrared. Flipper has a built-in ir transmitter and receiver. It comes preloaded with a massive database of infrared codes for TVs, air conditioners, projectors, soundbars, set-top boxes. Point it at any TV and try codes until one works. This is the feature that went viral on TikTok, people turning off TVs in public places. Harmless but annoying.

iButton and 1-wire. Some buildings use contact keys that look like metal buttons. The Flipper reads and emulates these through its ibutton connector. Old technology but still widely deployed.
BadUSB. Plug the Flipper into a computer via USB and it acts as a keyboard. It can type pre-written scripts automatically, running commands on the target machine. Pentesters use this to demonstrate how quickly a physical USB attack can compromise a workstation. The scripts use Ducky Script, the same language that the USB Rubber Ducky uses.
GPIO pins. The flipper has gpio pins that let you connect external modules, sensors, and debug tools. The video game module (a Raspberry Pi Pico add-on) turns it into a handheld game console. The WiFi dev board adds network scanning capabilities through an ESP32 chip. The gpio interface makes Flipper expandable in ways the base hardware was never designed for.
Bluetooth. BLE support allows the Flipper to communicate with phones and other Bluetooth devices. This module got attention after someone demonstrated Bluetooth Low Energy spam attacks at Midwest FurFest in September 2023, disrupting payment terminals and, more seriously, some medical devices in the area.
What Flipper Zero cannot do (despite what TikTok says)
The social media hype made Flipper sound like a universal hacking machine. It is not. Here is what it cannot do:
It cannot steal modern cars. Newer vehicles use rolling codes where every key press generates a unique encrypted signal. Capturing and replaying a rolling code does not work because the car has already moved to the next code in the sequence. Fixed-code systems from the 1990s and early 2000s are vulnerable. Anything made after 2005 with rolling codes? The Flipper cannot touch it.
It cannot clone encrypted NFC cards. Modern credit cards, newer transit passes, and most secure access badges use encrypted communication. The Flipper can read the UID (public identifier) but cannot extract the private keys needed to make a working clone. MIFARE DESFire, newer MIFARE Plus, and bank cards with dynamic CVVs are safe.
It cannot hack WiFi networks out of the box. The base Flipper has no WiFi hardware. The ESP32 dev board add-on can scan networks and run basic attacks, but calling it WiFi hacking is generous.
It cannot break through modern encryption. No brute-forcing WPA3 passwords. No decrypting AES-protected signals. The Flipper works with unencrypted or weakly encrypted protocols. Anything properly secured is beyond its reach.
The gap between what TikTok shows and what the device actually does is the source of most controversy. A teenager turning off a restaurant TV makes great content. A pentester finding that a corporate office still uses unencrypted 125 kHz badges for building access? That is the real use case that matters.
The controversy: bans, seizures, and government panic
Flipper Zero became the most controversial piece of consumer hardware since the lockpicking community went mainstream. Governments did not take it well.
In late 2022, US Customs seized 15,000 Flipper Zero units at the border. They were eventually released, but the seizure signaled that law enforcement saw the device as a potential threat. The FCC had no issues with it. Customs just wanted a closer look.
Amazon banned Flipper Zero from its marketplace in April 2023, classifying it as a "card skimming device." This was almost certainly wrong. The Flipper cannot skim card data in any meaningful way since it cannot extract private keys or dynamic CVVs. But Amazon's algorithms do not care about nuance, and the device disappeared from the platform.
Brazil's telecommunications regulator Anatel seized Flipper Zero shipments in 2023, blocking imports entirely. Brazilian buyers had to find alternative ways to get the device.
Gatwick Airport in the UK confiscated a Flipper Zero from a traveler in September 2023. Airport security apparently thought it was some kind of weapon. It measures 10 centimeters and has a cartoon dolphin on the screen.
The biggest showdown came in February 2024 when Canada announced plans to ban the Flipper Zero, linking it to car theft. The Canadian government's reasoning: car theft was increasing, Flipper Zero can interact with radio signals, therefore Flipper Zero is a car theft tool. Security researchers pointed out that the Flipper cannot beat rolling codes used in any car made in the last 20 years. The ban proposal was later walked back to targeting "illegitimate use" rather than the device itself.
A South Dakota Fusion Center police bulletin from August 2023 warned that extremists might use Flipper Zero to attack power infrastructure. Flipper Devices responded that modern power control systems are not vulnerable to the kinds of signals the Flipper transmits.
All of this panic has a common thread: regulators who do not understand the technology regulating it anyway. The Flipper Zero exposes insecurity that already exists. It does not create new vulnerabilities. If your office uses unencrypted RFID badges from 2005, that is your office's security problem. Banning the tool that reveals it does not fix the lock.
Custom firmware: Unleashed, Momentum, and the community
The official Flipper Zero firmware is deliberately conservative. It respects regional frequency restrictions and avoids features that could be classified as offensive. Some users wanted more.
Unleashed firmware removes regional frequency locks and adds sub-GHz protocols not included in the stock firmware. Momentum (formerly Xtreme) goes further with additional features, animations, and community-contributed protocol support. These custom firmwares are open source, community maintained, and easy to install via the Flipper's USB connection.
The Flipper app store (launched July 2023) adds another layer. Third-party developers build apps that extend the device's functionality. Everything from Bluetooth scanning tools to game emulators to specialized RFID utilities. The microsd card slot stores extra data, custom scripts, and firmware backups.
This open source ecosystem is what separates the Flipper from proprietary pentesting hardware that costs $500-$3,000. A professional Proxmark RFID tool runs $300+. A HackRF One for software-defined radio costs $300. A USB Rubber Ducky is $80. The Flipper does 80% of what these tools do, in one $169 package, with a community that keeps adding more.
The Flipper community on Discord and Reddit is one of the more active hardware hacking communities out there. People share custom scripts, protocol discoveries, and use case walkthroughs daily. The debate between official and custom firmware mirrors the jailbreak vs stock iOS argument. Official firmware keeps you legal everywhere and gets regular updates from the company. Custom firmware gives you tools that the company deliberately chose not to include. Most serious users install Unleashed or Momentum within the first week. The risk: custom firmware can violate local radio regulations since it removes the frequency restrictions that keep the official build compliant in different countries.
Who actually uses Flipper Zero (and who should)
Forget the TikTok pranksters. Here is who benefits from owning one:
Penetration testers use it on every engagement. Physical security assessments require testing badge clones, wireless access points, and USB attack surfaces. The Flipper covers all three without carrying a bag full of specialized equipment.
IT administrators test their own systems. Does the office NFC badge system use encryption? Does the conference room AV system accept any infrared command? Can someone walk up to a lobby terminal and run a BadUSB script? The Flipper answers these questions in minutes.
Students and hobbyists learn about radio protocols, hardware hacking, and embedded systems. The Flipper is an educational tool with enough depth to teach real security concepts. The gpio pins alone turn it into a basic logic analyzer and protocol debugger for electronics projects.
Home automation enthusiasts control devices from multiple brands with one gadget. If your garage uses 315 MHz and your ceiling fan uses infrared and your front gate uses 433 MHz, the Flipper handles all of them.
People who lose remote controls. Seriously. Program the Flipper with your TV's infrared codes and your gate's Sub-GHz signal and you never need another remote again.
Security researchers studying IoT vulnerabilities use it as a quick field scanner. Walk through a building and in 30 minutes you have mapped every wireless protocol in range: which badges use encryption, which doors run legacy RFID, which conference rooms have unsecured AV systems. That audit used to require a backpack full of gear. Now it fits in a pocket.
The sales numbers speak for themselves. Over one million units shipped by 2025. Revenue went from $25 million in 2022 to $80 million in 2023. That growth came from real demand across pentesting, education, and hobby markets, not just TikTok impulse buys. A lot of those units ended up in corporate security budgets next to Burp Suite licenses and Kali Linux installations.