Crypto Wallet Address Guide: Find My Wallet Address Safely
A wallet address is the closest thing crypto has to a street number. It tells the network where to drop your coins, and it is the one piece of information you must hand over every time someone wants to pay you. That makes it simple in theory and dangerous in practice. Type one character wrong, trust the wrong clipboard, or enter the address a piece of malware just pasted into your buffer, and the money is gone. Cryptocurrency transactions are not reversible. Your bank cannot call the other side and ask for a refund. A wrong wallet address is irreversible in almost every case, which is why a guide to wallet addresses belongs on every new holder's reading list.
This guide is written for the person who wants to send and receive crypto without losing a month's salary to a preventable mistake. It covers how a wallet address is a unique identifier on the blockchain, which formats exist, how to find my wallet address in the most common wallet apps, and the specific security habits that keep funds safe in 2026. Every rule here exists because real people lost real money ignoring it. Chainalysis put the share of stolen crypto value coming from individual wallet compromises at 44% in 2024, up from just 7.3% in 2022. Attackers are now targeting ordinary wallets far more than exchanges, and wallet address mistakes are the doorway.
What a Wallet Address Is and How It Works
Forget the jargon. A cryptocurrency wallet address is a unique string of letters and numbers, a pile of characters that basically says: drop my crypto assets here. A long wallet history just means you've been receiving into it for a while. Anyone on the blockchain network can send funds to it. Only whoever has the private key can move those coins out again, that person has access to your private balance, and nobody else does. The address itself is a unique string, different from every other address ever generated, and that uniqueness is what lets the network route payments correctly.
Picture it like a bank account. Your account number is the public bit, and a wallet address works like a bank account number in almost every way that matters. You hand it out freely, on invoices, in checks, in every payment form. Totally fine. Now think about your PIN. You'd never tell anyone. That's basically the public and private keys split, just with more math. The public address is like the account number. The private key is like the PIN. Share the first. Guard the second like it's your entire savings, because in effect it is. Share your wallet address when someone needs to pay you; never share your private keys with anyone, for any reason, ever.
Quick detour into the math, since it helps the rest make sense. Your private key is just a huge random number, 256 bits long, and if you ever had to type it out you'd be there all afternoon. Multiply it against an elliptic curve (secp256k1 for Bitcoin, Ed25519 for Solana, details you don't need) and out pops a public key. Hash that public key, chop it down, glue a checksum and a prefix on the front, and you have your wallet address. The whole chain only runs one direction. You can never, ever recover the private key from the address. That's the entire deal.
And the blockchain? It honestly couldn't care less who you are. No name fields. No email column. No passport number. Every transfer is recorded on the blockchain as a simple movement between two addresses, with an amount and a timestamp. Your address is pseudonymous, not the same as anonymous, because every move is permanent and public, but not attached to your real name either. Where does the link between "that 0x string" and "you, the person" usually come from? Two places. The KYC form you filled out at Coinbase or Binance. Or that one time you tweeted your address to a follower and forgot about it. The blockchain itself never told anyone. Handling a blockchain address safely starts with understanding that this is how wallet addresses work: public by design, private only if you stay careful.
Understanding Wallet Addresses Across Blockchains
Every chain writes addresses its own way. And the different wallet address formats do not mix. Not even close. An Ethereum wallet address will refuse Bitcoin. A Solana address will ignore USDT that was sent on Tron. Send to another wallet on the wrong chain and you usually lose the funds. No undo button exists. Your best friend in this whole mess is the prefix. Glance at the first few characters and you'll know which chain the address lives on. `bc1`. `0x`. `T`. `r`. `L`. Learn those five and you'll catch most wrong-chain mistakes before they happen. Bitcoin addresses cover the 1/3/bc1 family. ETH covers every EVM chain. The rest each live in their own corner.
So why this messy? Simple answer: nobody was coordinating. Each blockchain just picked its own encoding rules whenever it felt like it. Bitcoin started with Base58Check, then added Bech32, then Bech32m for Taproot. Ethereum chose plain hex with a mixed-case checksum glued on afterwards. Solana went with Base58 but dropped the checksum byte Bitcoin adds at the end. Deep down, the cryptography looks pretty similar everywhere. Elliptic curves, hash functions, the same handful of boring building blocks. But the packaging around those blocks is where every chain decided to do its own thing. Wallet software tries to hide all this from you. Mostly it works. Right up until it doesn't.
Here's a thing that surprises people. One seed phrase can run dozens of wallets across dozens of chains at once. Modern crypto wallets generate a fresh unique wallet address for every type of cryptocurrency you hold, and they all trace back to the same 12 or 24 words you wrote down at setup. Open a multi-chain wallet that supports BTC, ETH, and SOL, and you'll see three completely different strings. Each on its own ledger. Moving coins on one does absolutely nothing to the others. How is this possible? A small pile of standards does the work: BIP32, BIP39, BIP44. Of those, BIP44 is the one that defines the derivation path, so a single phrase cleanly maps to a Bitcoin wallet address here, an Ethereum wallet address there, a Solana address over there. Really convenient. Also a brutal single point of failure. Lose the phrase and everything downstream disappears with it.
Types of Crypto Wallet Address Formats in 2026
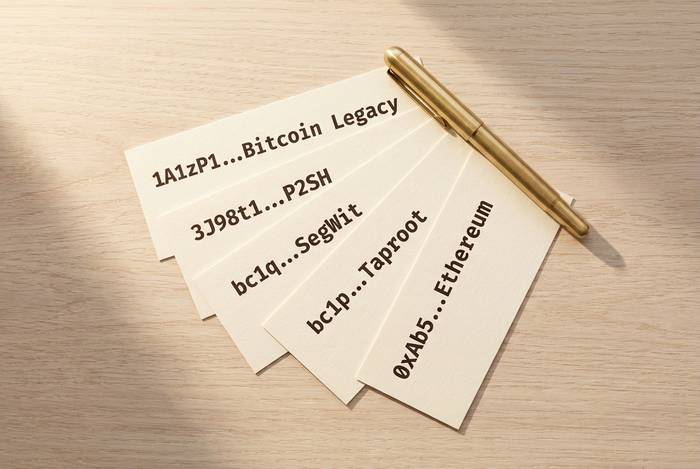
Here are the main wallet address formats you'll actually run into. Learn to recognize the prefix at a glance and you'll catch a surprising number of mistakes before they happen.
| Chain | Format | Prefix | Length | Notes |
|---|---|---|---|---|
| Bitcoin | Legacy P2PKH | `1` | 26–34 | Oldest format, still valid |
| Bitcoin | P2SH | `3` | 34 | Script hash, often multisig |
| Bitcoin | SegWit Bech32 | `bc1q` | 42 | Lower fees, lowercase only |
| Bitcoin | Taproot | `bc1p` | 62 | Latest format, privacy-enhanced |
| Ethereum | EVM hex | `0x` | 42 | Same format on Polygon, Arbitrum, Base |
| Solana | Base58 | `(no prefix)` | 32–44 | Case-sensitive |
| Tron | Base58Check | `T` | 34 | Used for TRC20 USDT |
| Litecoin | Legacy / Bech32 | `L`, `M`, `ltc1` | 26–62 | Similar to Bitcoin |
| XRP (Ripple) | Base58 | `r` | 25–35 | Requires destination tag on exchanges |
| Dogecoin | Legacy | `D` | 34 | Bitcoin fork inheritance |
Bitcoin is the messy one. Four flavors of bitcoin wallet addresses, because the network kept adding new formats without breaking the old ones. Legacy addresses starting with 1 are the original pay-to-public-key-hash format from 2009. Still valid. Still works. Still the slowest and most expensive to spend from. Addresses starting with 3 are pay-to-script-hash, added back in 2012 to support multisig and other script-heavy tricks. SegWit Bech32 addresses starting with bc1q landed in 2017 via BIP 173. Taproot Bech32m addresses starting with bc1p followed in 2021 under BIP 350. Why did BIP 350 exist at all? Because Bech32 had a quirk: trailing p characters let attackers sneak q characters in or out undetected. Not the kind of bug you want in the address format for a currency. All four types are valid today, they charge different fees, and a few old services still cannot send to the newer ones. Which is its own kind of hazard.
Ethereum took an easier route. Just one format. 0x followed by 40 hex characters. That's it. The same 0x string works on Ethereum, Polygon, Arbitrum, Base, Optimism, anything that speaks EVM. On top of that Ethereum layers a mixed-case checksum defined in EIP-55, which capitalizes certain letters based on the keccak-256 hash of the lowercase address. Mistype a single character? The checksum usually catches it. The spec puts it at roughly 99.9753% of random single-character typos, which is a nice number and yes I had to look it up. But here's the trap. Because the same 0x address is valid on every EVM chain, it's dangerously easy to send USDC on Ethereum mainnet to that 0x address and expect it to show up on Polygon. It won't. Each chain has its own ledger. Each one has its own copy of the USDC contract. They don't talk to each other. This BEP20 vs ERC20 screw-up is one of the most common loss scenarios in exchange support tickets. Full stop.
How to Find My Wallet Address in Any Wallet App
This feels harder than it is. Genuinely. The button is labeled differently in every app, but the process to get a crypto wallet address is the same four steps everywhere in 2026.
1. Open your wallet. Pick the coin, whichever crypto asset you want to receive crypto in, BTC, ETH, SOL, doesn't matter.
2. Find the Receive button. Some apps call it Request. Some call it Deposit. Same thing.
3. A screen pops up with your address written out as a string of letters and numbers, plus a QR code underneath.
4. Copy the string, or just show the QR code to the person paying you. Done. That's how to find your wallet address and receive funds in any modern wallet.
Most wallet applications in 2026 follow those same four steps, whether you're on a phone, a desktop, or a browser extension.
Hardware wallets work a little differently, and honestly this is where real self-custody security lives. Running a Ledger or a Trezor? You go through the same flow in Ledger Live or Trezor Suite on your computer, but the device itself also flashes the receiving address on its own tiny screen. Always look at that screen. Always. Match it to what your computer shows. If they disagree by even a single character, stop what you're doing. Your computer has malware on it. I'm not exaggerating, that mismatch is exactly what a clipboard hijacker produces, and the only reason you caught it is because the hardware wallet's display lives on its own little chip that your infected browser can't reach.
Software wallets like MetaMask, Trust Wallet, Phantom? The address is right at the top of the main screen, or a tap away under Receive. Copy and paste, no drama. For exchanges, Coinbase, Binance, Kraken, all of them, you'll find the address inside a Deposit menu. A nice touch at most exchanges: they hand you a fresh unique address every time you request one. Leave that feature on. It's a small privacy win for zero effort, and it protects your digital asset balance by making chain analysis harder.

How to Use Crypto Wallets and Send a Transaction
The flow to use crypto wallets for sending crypto is almost universal. You tap Send, paste or scan the recipient’s wallet address, choose the amount, review the fee, and confirm. The blockchain then broadcasts the transaction, miners or validators include it in a block, and within minutes or hours the recipient sees the funds arrive. Sending and receiving cryptocurrencies is simple mechanically. The risk is entirely in the middle steps, and every loss caused by sending crypto to the wrong address happened because someone rushed one of them.
Three things matter before you hit confirm. First, make sure the correct wallet address exactly matches what the recipient gave you. Second, make sure the chain matches. Sending USDT on Ethereum to a Tron USDT address is the classic way to lose money through a trivial mismatch, and exchanges often use different address formats for the same token across networks. Third, check the fee. Overpaying is wasteful; underpaying can leave a crypto transaction stuck for days.
A good habit for larger transfers is a test transaction. Send a very small amount first, wait for it to arrive, and only then send the full amount. The few cents in network fees you spend are a cheap insurance policy, and they are the single best defense against typos, copy-paste failures, and the address-poisoning attacks described later in this guide.
Sharing Your Wallet Address Safely Without Risk
The address is public. Fully, unambiguously public. Safe to share with anyone who needs to pay you, safe to post on your website, safe to print on your invoice. A wallet address cannot be used to steal your funds, only the private key can do that, and the whole point of asymmetric cryptography is that one side of the pair is meant to be shouted from rooftops while the other is meant to be carried to the grave.
So what's the catch? The catch is privacy and phishing, not balance loss. Publish your ETH address publicly and anyone with a block explorer can look up your balance, your full transaction history, every NFT you've ever touched, every shady DeFi protocol you tried once and regretted. Share it in a Telegram group and every participant sees it. On-chain analytics in 2026 is a mature industry with good tooling and sharp people. For a wallet with a long history, address reuse amounts to publishing a financial diary with your name on the cover.
And then there's the golden rule, which doesn't get less true with repetition: never share your private keys, your seed phrase, or your recovery words. Not with a support agent. Not with an airdrop bot. Not with a "Ledger rep" who emailed you about a firmware update. Not with your best friend. Literally nobody legitimate needs them. I've watched people lose five-figure balances because a DM from "customer service" felt helpful and official. It wasn't. It never is. Never share your private keys to anyone for any reason.
The Wrong Wallet Address Problem: Avoid Lost Funds
Send crypto to the wrong wallet address and, almost every time, the money is gone. There is no customer service department for a blockchain. No chargebacks, no fraud protection, no friendly clerk who can reverse the transaction. The ledger does what you told it, even when what you told it was a typo.
The ways people actually lose funds are weirdly boring. Hand-typing an address used to be the main villain, but nobody in their right mind types 42 hex characters anymore, so this barely happens in 2026. Clipboard hijacking does. A whole family of Windows trojans called "clippers", Laplas Clipper being the most famous, sold as malware-as-a-service for around $549 a year, quietly watches your clipboard and swaps any crypto address you copy with an attacker's lookalike address. You paste, you hit send, and it looks completely normal. Microsoft coined the term "cryware" for this entire category, and they track hundreds of thousands of infections a year.
Then there's address poisoning, which is newer and genuinely cruel. The attacker generates a vanity address matching the first four and last four characters of an address you transact with often. They send you a dust transaction (or a zero-value one) so their fake address appears in your wallet history. Next time you need that address, you lazily copy from history, and grab the attacker's version instead. A Carnegie Mellon CyLab study published in early 2025 logged around 270 million on-chain poisoning attempts hitting 17 million victims between July 2022 and June 2024, with at least $83.8 million in confirmed losses. That's not a fringe threat anymore. That's industrial-scale phishing.
The most infamous single case happened on 3 May 2024. A whale lost 1,155 WBTC, roughly $68 million at the time, to a poisoned lookalike that matched their usual destination at both ends. The attacker returned the bulk of the funds a week later for reasons still debated in the community, but even sophisticated users who should have known better fell for the history-copy trick. In December 2024 another trader got caught the same way and lost close to $50 million in USDT. Different people, different blockchains, same lazy habit: trusting transaction history as a source of addresses.
| Mistake | How it happens | How to prevent it |
|---|---|---|
| Typo | Hand-typing a long address | Always copy-paste or scan QR |
| Clipboard malware | Malware replaces copied address | Verify on hardware wallet screen |
| Address poisoning | Lookalike address in history | Copy from contacts or fresh source |
| Wrong chain | USDT sent on ERC20 vs TRC20 | Match chain exactly before sending |
| QR spoof | Fake QR code in public | Verify first and last 6 characters |
Every one of these mistakes is prevented by the same core habit: always double-check the address before sending, and verify it on a device the malware cannot touch. Copy, paste, and then compare the address exactly character by character, at least the first six and last six, against the original source. An incorrect address the right wallet app would have sent to is impossible to recover once the signature is broadcast. For high-value transactions, a hardware wallet is the right wallet, because its screen is isolated from the computer and cannot be tampered with by software.
Bitcoin and Ethereum both protect against simple typos with built-in checksums. Bitcoin uses Base58Check, so a single wrong character in a legacy address will usually fail the checksum and refuse to send. Ethereum adds EIP-55 mixed-case checksums to catch the same kind of error in 0x addresses. These checksums do not help against malicious swaps, because the attacker's address is also a valid correct address. They only help against honest typos.
Managing Wallet Addresses and Privacy on Chain
Managing wallet addresses is easy mechanically and complicated privately. On a chain like Bitcoin, best practice is to generate a new address for every incoming payment. Doing so breaks the link between payments and makes it harder for an outside observer to trace how much crypto you hold. Reusing the same address repeatedly ties every payment to the same blockchain identity and gives anyone with a block explorer a complete view of your activity.
Ethereum is different. Because every Ethereum address is also an account with a nonce and a balance, most people and most apps use one address for everything. This is convenient, but it is the reason chain analysis is so effective on Ethereum. If you want privacy, a fresh address per project is the minimum. Mixers and privacy tools add more protection but raise compliance flags on many exchanges.
Whitelisting is the other big lever. Most exchanges and many hardware wallet flows let you whitelist trusted addresses so that funds can only be sent to a pre-approved destination. Combined with a waiting period on new entries, whitelisting is one of the cleanest ways to block both clipboard malware and account takeovers, because the attacker cannot simply swap in a fresh address.
Address books, contacts, and wallet name services like ENS make daily life easier by replacing a 42-character hex string with a memorable label like `alice.eth`. These labels are convenient but phishable. Unicode homograph attacks register a domain whose glyphs look identical to a trusted name but use Cyrillic or Greek lookalike characters, and the victim copies an address resolved from the fake name without noticing. The class of attack has been documented for two decades on the web, and crypto wallets that auto-resolve ENS, SNS, or Unstoppable Domains inherit the same risk. Always resolve an ENS name the first time through a trusted interface, confirm the underlying address matches the person you expect, and save it in your own address book after verification.
Dust attacks are a related trick that often comes before poisoning. An attacker broadcasts tiny transactions to thousands of addresses so that when the victim later consolidates their unspent outputs, the dust travels with them and reveals the cluster of addresses belonging to the same owner. The May 2024 WBTC victim was monitored via dust for weeks before the real attack landed. Wallets like Wasabi, Samourai, and Sparrow now let you mark dust as "do not spend" to break the link.
Handling Wallet Addresses: Security Rules for 2026
Defending against the three big threats, clipboard malware, address poisoning, wrong-chain transfers, comes down to a handful of habits you either do or you don't. Here they are, short on purpose.
Use a hardware wallet for anything you can't afford to lose. Not optional, not a luxury, not paranoia. A Ledger or a Trezor gives you a little physical screen that malware on your computer literally cannot reach, and verifying the receiving address on that screen before you sign blocks the overwhelming majority of clipboard attacks. Buy from the official store, not eBay. In November 2024, Ledger Donjon published a voltage-glitching disclosure against the Trezor Safe 3 microcontroller, which only matters if someone has physical access to your device, but that's exactly what a tampered second-hand device gives them.
Turn on address whitelisting wherever your exchange supports it. Set the trusted destinations once, leave the waiting period cranked up, eat the friction. Most account-takeover drains involve the attacker swapping out the withdrawal address, and a whitelist blocks that attack path cleanly. Tiny cost, huge payoff.
Run a test transaction every time you're sending somewhere new. A few cents in fees versus losing the whole payment to a BEP20/ERC20 mixup, do the math. Send a small amount, wait for it to confirm, check it arrived, then send the main transfer. This one habit catches typos, clipper malware, wrong-network selection, and the odd exchange bug, all at once.
Keep your wallet apps and browser extensions updated. Outdated versions are where most public exploits still work, and a fake MetaMask update is one of the classic ways to replace a legitimate wallet with a compromised clone. Patch when prompted. It's boring. It still blocks a huge share of real-world losses.
And one more time, because repetition is the only thing that sticks: share your public wallet address freely, never ever share your private keys, your seed phrase, or your recovery words. No exceptions. The day someone asks you for your seed phrase is the day you are being scammed, even if they're polite about it.




