What Is a Nonce in Crypto? Bitcoin Mining, Ethereum, Cryptography

In December 2010, on a stage at the Chaos Communication Congress in Berlin, a small group called fail0verflow announced that they had extracted Sony's master signing key for the PlayStation 3. The exploit did not break a 256-bit elliptic curve. It did not crack AES. It exploited the fact that Sony's code-signing system reused the same number for every signature it produced. That number was a nonce.
The same word, "nonce," shows up in three corners of the crypto world that have almost nothing else in common. It is the variable a Bitcoin miner cycles through trillions of times a second hunting for a valid block hash. It is the counter your Ethereum wallet uses to sequence outbound transactions, and the reason a stuck transaction blocks every later one you sign. It is the unique value an AES-GCM cipher needs to keep two encrypted messages from leaking each other's contents. One word, three jobs, none of them interchangeable. Mistaking one for another is how newcomers misread "nonce too low" errors, how miners design impossible setups, and how systems like the PS3 lose their root of trust.
A 32-bit nonce called "number used once": origin
The backronym is everywhere. "Nonce stands for number used once." Roughly true, historically wrong. The English word predates the cryptography by some 750 years. "For the nonce" turns up in Middle English manuscripts around the 1200s. It meant "for this particular occasion."
Cryptography borrows the word in 1978, with the Needham-Schroeder authentication protocol. There the defining property is not randomness. It is uniqueness, inside a defined scope. Wikipedia, deferring to actual practice, calls a nonce "an arbitrary number that can be used just once in a cryptographic communication." A counter qualifies. So does a timestamp. So does a random value, or any blend of the three. What matters is that, inside the system, the same nonce never reappears with the same key, or against the same context.
One word does the work, and the work splits three ways. Bitcoin's mining nonce varies until the block hash drops below the difficulty target. Ethereum's account nonce is a counter that the network refuses to let repeat. A cryptographic nonce in symmetric encryption is a value paired with a key, and reusing it once tears the encryption open.
The word is loose. The contexts are not.
How the nonce works in Bitcoin mining
In Bitcoin, the nonce occupies a 32-bit field inside the 80-byte block header. Four bytes. Values run from zero to 4,294,967,295. Just under 4.3 billion possible numbers, which sounded enormous when Satoshi wrote the protocol and is now exhausted by a desk-sized ASIC in microseconds.
Mining is a race to find a value in that field that produces a valid block hash. Take the 80-byte header. Feed it through SHA-256, the cryptographic hash function the bitcoin blockchain runs on, twice. Out comes a 256-bit number. Compare that number to the target hash set by the network's difficulty target, the consensus mechanism that drives proof-of-work. Below the target? Block valid, miner wins. Above the target? Bump the nonce by one and rehash. Bitcoin miners loop this until someone finds a valid nonce and the new block gets added to the blockchain.
Why such a small field for so large a job? Structural reasons. The nonce is the cheapest piece of the header a miner can mutate. Every other field has dependencies. The merkle root summarizes the block's transactions, so changing it forces the whole transaction tree to recompute before a new hash can be tried. The nonce sidesteps all of that. Each hash attempt is independent. Incrementing the nonce gives no closer advancement than picking a random value would. Brute force, dressed in consensus language.
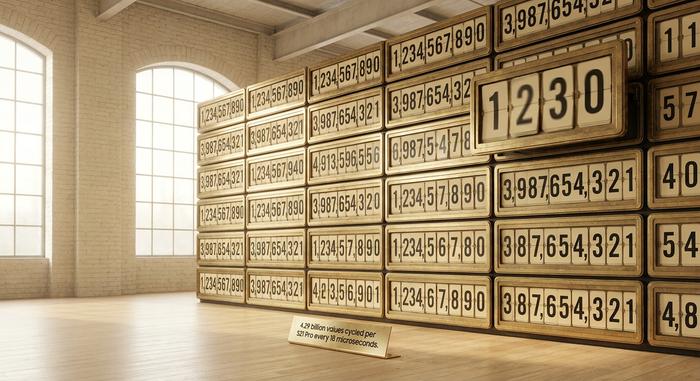
The design held up for roughly a year. Then ASICs broke it. Modern miners exhaust the entire 4.3-billion nonce space in microseconds, not seconds. A Bitmain Antminer S21 Pro runs at 234 terahashes per second. The full nonce field exhausts on that hardware in about 18 microseconds. As of May 2026, the bitcoin network's total hashrate sits near 996 EH/s, with difficulty at 132.47 trillion. A single S21 Pro chews through every possible nonce value tens of thousands of times per second on its own.
So Satoshi's protocol leaves the miner two clean exits once the 32-bit space exhausts. The first is the "extra nonce," a field tucked inside the coinbase transaction's scriptSig. BIP34 codifies it. Two to one hundred bytes, miner-controlled. Mutate the extra nonce and the coinbase TXID changes, the merkle root has to be recomputed, the block header changes, and a fresh 32-bit nonce search opens up. The second exit is to bump the timestamp or rotate the version bits within the protocol's allowed range. Mining pools today cycle all of them as part of normal operation. Adjusting the nonce is the cheapest mutation. Adjusting the extra nonce is the second-cheapest. The merkle and timestamp rotations sit further out, in order of how much work each costs to recompute.
When somebody lands a hash below the target — miners call it the "golden nonce" — the new block flies out across the peer-to-peer network, and every competitor drops their current search to start over on the next round.
| ASIC model | Hashrate | Time to exhaust 32-bit nonce | Efficiency |
|---|---|---|---|
| Antminer S21 | 200 TH/s | ~21 µs | 17.5 J/TH |
| Antminer S21 Pro | 234 TH/s | ~18 µs | 15 J/TH |
| Antminer S21 XP | 270 TH/s | ~16 µs | 13.5 J/TH |
A real, recent example anchors the abstraction. Block 948,000, mined in early 2026, has block hash `00000000000000000001b01841afc366a4f999b291c8563ee0d0db956fc2db44` and a winning nonce value of 2,582,463,598. That single integer, combined with the rest of the block header, produced a hash low enough to be added to the blockchain. Every other nonce its miner tried that round produced something too large.
This is what proof of work is, mechanically. Not a puzzle in the riddle sense. A search for a valid nonce, paid for in electricity.
Hash nonce vs account nonce: same word, different job
The word "nonce" gets reused for one more thing in cryptocurrency, and the overlap is the single biggest source of confusion among newcomers. Bitcoin's mining nonce is a search variable. Ethereum's account nonce is a counter. They share a name and almost nothing else.
| Hash nonce (Bitcoin) | Account nonce (Ethereum) | |
|---|---|---|
| Job | Search for a valid hash below target | Sequence outbound transactions per account |
| Where it lives | Block header (32 bits) | Account state (full integer, starts at 0) |
| Who mutates it | The miner, in hardware, billions per second | The wallet, automatically, one per send |
| What "wrong" means | Lottery ticket fails, try the next nonce | Transaction is rejected or stuck |
| Tied to consensus? | Yes, this is proof of work | No, this is replay protection |
A hash nonce is a temporary number a miner throws away. An account nonce is permanent state etched into the network's view of your address. Confusing one for the other — treating the blockchain nonce of a Bitcoin block as if it were a sequence counter — is how people read an Ethereum "nonce too low" error and assume their mining setup is broken. Different blockchains, different jobs, same word. Even within a single ecosystem, the role of a nonce in blockchain operations depends entirely on whether you are watching the consensus layer or the account layer.
Ethereum account nonce and the stuck-transaction problem
Every externally owned account on Ethereum carries its own nonce. The counter starts at zero, the first time the address ever sends a transaction. From there it climbs by one for each transaction that lands in a block. When you send something, your wallet asks the network for the current value, attaches the next number in line, and signs. The network only accepts the outbound queue in strict order. Nonce 0, then 1, then 2. Gaps are not allowed.
This strict ordering is what gives Ethereum its replay protection. A signed transaction binds to one specific nonce, and since EIP-155, also to one specific chainID. An attacker cannot rebroadcast an old executed transaction as if it were new. By the time the rebroadcast arrives, the account nonce has already advanced past it. The chainID kills cross-chain replays in the same swing. Inside one chain, a confirmed transaction lives at one point on a counter that has already moved on.
The same rigid ordering produces the pain point new Ethereum wallets keep running into. A transaction goes out with too low a tip. Validators pass it over. The mempool drops it from the priority queue. The transaction now sits in limbo — not confirmed, not failed, just stranded. Worse, every later transaction the same address signs picks up a higher nonce. The network refuses to touch any of them until the stranded transaction either confirms or gets replaced. One slow transaction stalls the whole queue.
The fix lives in a mechanic called replace-by-fee. Your wallet rebroadcasts a fresh transaction at the same nonce as the stranded one, but with more gas. EIP-1559, the gas-pricing model that has run Ethereum since the London upgrade in August 2021, sets the rule: the new transaction must raise both `maxFeePerGas` and `maxPriorityFeePerGas` by at least ten percent over the original. Want to kill the stranded transaction outright instead of replacing it? Send a zero-ETH self-transfer at the stuck nonce, with a higher tip. The slot consumes itself, and every later transaction in the queue is unblocked.
The May 2026 numbers, for context. Average priority tip near 1.875 Gwei. A standard 21,000-gas cancellation lands around $0.05 on a calm day, and climbs into the low dollars during congestion. There is one lesson everyone eventually learns the hard way: always replace the lowest pending nonce first. Bumping the fee on a later transaction while its predecessor still sits stuck accomplishes nothing at all.
Account abstraction reshapes this story a little. ERC-4337 smart accounts use a 2D nonce, splitting the integer into a 192-bit "key" and a 64-bit sequence. Different keys form parallel transaction streams. A stalled batch on one key does not block work on another. The account nonce has finally grown past being a single linear counter.
One last myth worth killing. Ethereum's transition to proof of stake at the Merge, in September 2022, did not remove the account nonce. What disappeared was the mining nonce inside the block header, because validators get picked by slot now rather than by a hash puzzle. The account nonce stayed exactly where it always lived, in the account state trie.
Cryptographic nonce in encryption: the catastrophic version
Step outside blockchain and the cryptographic nonce does a sharper job. Get it wrong, and the floor falls out from under you.
Every modern authenticated cipher pairs a secret key with a per-message nonce. AES-GCM, the workhorse inside TLS 1.3, uses 96 bits. NIST SP 800-38D wrote the spec. ChaCha20-Poly1305, the alternative codified in RFC 8439 (June 2018), copies the same 96-bit nonce length and pairs it with a 256-bit key. The rule under both, in plain English: each (key, nonce) pair runs exactly once. Reuse is not a soft degradation. It is a cliff.
What does the cliff look like? Reuse a nonce in AES-GCM under one key. Pretend an attacker has captured both ciphertexts. They XOR the two together. Out drops the XOR of the two underlying plaintexts. Confidentiality, gone in one step. Worse follows. GCM's authentication mode leaks its internal authentication subkey — the value that signs every ciphertext under that key. With the subkey in hand, the attacker writes new authenticated ciphertexts and the legitimate receiver accepts them as real. A state-of-the-art cipher, on one bad nonce, slips below a Caesar shift.
None of that is hypothetical. A 2016 USENIX WOOT paper, "Nonce-Disrespecting Adversaries," scanned production HTTPS endpoints and turned up 184 servers reusing GCM nonces. The buggy builds included specific Cisco IOS XE images and Radware ADC firmware. CVE-2016-0270 and several adjacent CVEs track them.
Sony's PS3 break in December 2010 was the same disease in a different cipher: ECDSA. Every ECDSA signature needs a per-signature value, written as k, that is unique and secret. Sony's signing code skipped the unique part. It hardcoded a constant k and reused it on every signature. Give an attacker two ECDSA signatures over different messages with the same k, and they have two linear equations in two unknowns. Solve. Out comes the private signing key, in closed form. fail0verflow walked through this onstage at the 27th Chaos Communication Congress in Berlin. Sony's master signing key hit the open Internet within hours. Every PS3 ever made lost its chain of trust at once.
The deterministic fix, codified as RFC 6979 in 2013, takes the random number generator out of the process. Derive k from an HMAC of the message and the private key. Same message, same key, same k — no RNG to corrupt. Modern Bitcoin libraries ship deterministic ECDSA as the default.
Two corollaries follow from these stories, and they often confuse developers. With AEAD ciphers (AES-GCM, ChaCha20-Poly1305), a predictable nonce is fine. A counter works. Uniqueness is the entire requirement. With ECDSA and Schnorr signatures, the rule flips. A predictable k is catastrophic. The signing nonce there has to be unique, unpredictable, and secret at the same time. Mixing the two camps is exactly how nonce-reuse bugs keep appearing in custom wallet code. The Kopia backup project's 2024 audit logged a random GCM-nonce collision risk on long-running keys, and pentesting reports on newer SDKs file similar findings month after month.
Nonce vs salt vs IV: avoiding the three-way confusion
People throw three words around in security writeups as if they meant the same thing. Salt. Nonce. IV. They are not synonyms.
Salt belongs to password hashing. You take a per-user random value, mix it into the hash, and now precomputed rainbow tables for "password123" stop working against your database. A salt sits in plaintext next to the hash. Nobody hides it. Two users sharing a salt is awkward; it lets an attacker who cracks one cracked their twin too. It is not the end of the world.
Nonce belongs to messaging and signatures. Per-message in symmetric encryption. Per-signature in ECDSA. AEAD ciphers like AES-GCM expose the nonce in the clear, the way a salt sits next to a hash. ECDSA hides it, treats it as a secret, and demands fresh randomness each time. Either way, collisions are not awkward. They are fatal. The whole guarantee, gone.
IV — short for initialization vector — is the legacy name for what newer specs call a nonce. CBC and CTR modes used the word for years. Modern AEAD documentation switched, mostly because "vector" sounded like math homework and people kept reusing them. "Nonce" leans harder on the rule.
Need one rule that fits on a sticky note? A salt protects a secret you are storing. A nonce protects a secret you are sending.

Why the nonce matters beyond bitcoin mining trivia
A nonce is a small object. Thirty-two bits in Bitcoin. A counter in Ethereum. Twelve bytes in AES-GCM. It carries a disproportionate weight for its size. For ordinary users, every stuck Ethereum transaction, every TLS handshake to a banking site, every signature a hardware wallet produces depends on a nonce being handled correctly. For developers, nonce mishandling is the most common entry point for catastrophic bugs in custom cryptographic code. The PS3 incident was an extreme case, but the same failure mode keeps appearing in newer wallet SDKs and backup tools. For Bitcoin's economics, the 32-bit nonce combined with the extra-nonce mechanic is what made ASIC mining a fair lottery in the first place. One of Satoshi's most consequential design choices, hidden in plain sight inside an unremarkable header field.
A nonce is the thing that says this happened once, in this order, exactly this way. Strip it out, and every system that depends on uniqueness collapses into something an attacker can rebuild on the cheap. Consensus breaks. Replay protection vanishes. Encryption leaks. Signatures forge.

