What Does Permissionless Mean? A Crypto Concept Unlocked

Ask someone to explain blockchain. Within thirty seconds, "permissionless" lands. The word sounds like jargon. People drop it like everyone knows the definition already. Half of why crypto matters sits underneath it.
But what does it really mean? Just this: you need nobody's approval to use a blockchain. No approval to run a node. No approval to write a contract. No approval to send your tokens to your friend in Lagos. Zero signup forms. Zero KYC at the protocol layer. No bank to ring up. Got a wallet and the internet? You are a full participant. That one engineering call separates Bitcoin and Ethereum from SWIFT, Visa, Fedwire, take your pick. And it ripples through DeFi, NFT markets, the censorship-resistance debate, all of it.
We will walk through what permissionless actually means in practice, how it plays out, where it splits from permissioned options like Hyperledger Fabric and R3 Corda, and why the distinction does real work in 2026.
What Permissionless Really Means in Crypto
A permissionless system is one where access does not hinge on a gatekeeper's approval. In crypto, that translates into a short list of concrete rights anyone holds by default. Join the network. Send and receive transactions. Run a node. Read every transaction ever made. Copy or fork the open-source code. Mine or stake to participate in consensus. Pick any of those, and you do not need anybody's permission to start.
The word "permission" is doing real work here. Take SWIFT or Visa. Every actor on those rails has been vetted in advance. Banks belong to a closed club. Merchants sign onboarding agreements. Customers pass identity checks. There is no path for some anonymous individual in a country with broken banking to plug directly into the network and start moving money. The infrastructure literally does not let them.
A permissionless blockchain flips that. The protocol code does not know who you are. It does not care. Bitcoin's full nodes will accept any valid transaction from any address, anywhere. Ethereum's validators will include any signed message that pays the gas fee. No bank in the consensus loop. No regulator. No corporate compliance team. Those actors do exist around the system, sure, especially at fiat on-ramps and centralized exchanges. But inside the protocol itself, they have zero power.
This is the technical foundation under self-custody, censorship-resistant payments, open DeFi, all of it. Trace any of those features back to source, and you land on permissionlessness.
How Permissionless Blockchains Work in Practice
A permissionless blockchain stays standing because software on thousands of independent computers enforces the rules, not an admin with override powers. For the system to hold, three things need to be simultaneously true.
One: anyone with hardware can run a node. Bitnodes counts roughly 22,992 reachable Bitcoin nodes worldwide as of late April 2026. Ethereum's consensus layer is up to about 2.25 million active validators post-Merge. Every node, every validator, independently checks every transaction against the consensus rules. A rogue node tries to cheat? The rest of the network drops its blocks.
Two: anyone can submit a transaction by paying the network fee. Hedge fund pushing millions or a college student testing a contract on Sepolia, doesn't matter. The transaction lands in the same mempool, sits in the same queue, gets included under the same rules. Address-level discrimination at the protocol layer is technically impossible.
Three: the source code is open. Bitcoin Core and Ethereum's reference clients live publicly on GitHub. Anyone can read it. Anyone can propose changes through Bitcoin Improvement Proposals or Ethereum Improvement Proposals. Anyone can fork the project, anyone can build a new chain on top. The Federal Reserve's 2024 governance note documented how informal this gets: roughly five core maintainers carry most of Bitcoin's commit weight, while Ethereum runs with a wider, more visible developer community fronted by figures like Vitalik Buterin.
That stack is where permissionless networks get their odd resilience. No headquarters to raid. No API key to revoke. No compliance officer who can flip a switch and disable accounts. The system keeps going whether one country bans it, an exchange goes bankrupt, or a key developer disappears.

Permissioned vs Permissionless: A Direct Comparison
Not every blockchain is permissionless. A permissioned blockchain looks structurally similar but locks the door at the participation layer. Only vetted, identified parties can run nodes or submit transactions. The most common implementations are Hyperledger Fabric, R3 Corda, JPMorgan's Quorum, and Microsoft's Azure Blockchain Service before its 2021 retirement.
Both architectures use distributed ledgers. Both can hold smart contracts. The split is about who gets in.
| Feature | Permissionless | Permissioned |
|---|---|---|
| Access | Open to anyone | Vetted parties only |
| Identity | Pseudonymous addresses | KYC-verified entities |
| Consensus | Proof-of-Work or Proof-of-Stake | PBFT, RAFT, IBFT (lightweight) |
| Throughput | Lower (Bitcoin ~7 TPS, Ethereum ~30 TPS) | Higher (Hyperledger 1,000-3,000+ TPS) |
| Energy use | High on PoW chains, low on PoS | Low |
| Transparency | Full ledger public | Selective, often private |
| Censorship resistance | Strong | Weak by design |
| Compliance flexibility | Limited at protocol level | Built-in (AML, GDPR, MiCA) |
| Best for | Money, public coordination, DeFi | Supply chains, settlements, regulated finance |
The permissioned model is not a failed version of the permissionless one. It is a different tool for different problems. A bank consortium settling overnight transfers among 30 known members has zero need for a stranger from anywhere on Earth to validate their blocks. They want speed, identifiable counterparties, and clean compliance reporting. A permissioned chain delivers all three.
A permissionless protocol cannot. By definition it sacrifices throughput and identity verification in exchange for openness. Trying to "fix" Bitcoin to handle Visa-scale TPS with full KYC would mean turning it into something that is no longer Bitcoin.
Bitcoin and Ethereum as Permissionless Protocol Models
Bitcoin and Ethereum are the two reference designs every other permissionless protocol copies or reacts against. They share the same permissionless properties. They execute them in radically different ways.
Bitcoin keeps the protocol stable on purpose. Big changes? Rare. They go through soft forks. High social consensus required, no shortcuts. The Federal Reserve note treats this stability as a governance choice in itself. The Bitcoin community treats minimal change as a feature, not a bug. Result: a protocol running pretty much the same way since 2009, with predictable monetary policy and a small, concentrated developer pool. Five-ish core maintainers carry most of the day-to-day commit weight. Many of them under pseudonyms.
Ethereum picked the opposite road. Major coordinated hard forks have reshaped the network repeatedly. 2016 DAO recovery fork. 2021 EIP-1559, restructuring gas fees. 2022 Merge, swapping proof-of-work for proof-of-stake. Ethereum accepts more frequent change because its application layer (DeFi, NFTs, rollups) demands more functionality. The price is occasional contentious splits. The 2016 fork left a minority chain alive, still trading as Ethereum Classic.
Both networks lean on off-chain governance. Improvement proposals (BIPs and EIPs). Public discussion forums. Mailing lists. Software review. Neither runs on-chain voting the way some newer chains do. Decisions emerge from rough consensus across developers, validators or miners, and node operators. Messy by design. And the messiness is what makes capture by any one actor genuinely difficult.
Permissionless DeFi: The Open Financial Layer
DeFi is where you see permissionlessness in practice. Lending markets like Aave and Compound. DEXs like Uniswap and Curve. Stablecoin issuers like MakerDAO. All of them are permissionless smart contracts on Ethereum and other chains. Anyone supplies liquidity. Anyone takes a loan against collateral. Anyone mints synthetic assets. Anyone swaps tokens. Zero signup. Zero credit check.
How big is it? Total value locked across permissionless DeFi sits around $95-140 billion in early 2026 per DeFiLlama, back near the 2021 peak after the 2022-23 drawdown. Ethereum alone holds roughly $57 billion. Aave V3 leads the lending category with about $26.2 billion in deposits. Lido secures around $23 billion in liquid-staked ETH on its own. The numbers matter because they prove real users park real money inside systems they cannot phone up.
The implications go past yield farming. A permissionless lending protocol does not check your nationality before approving a loan. It does not freeze your account because your name pings a watchlist. It does not need a credit score, which 1.4 billion unbanked adults globally cannot produce. The protocol just verifies that collateral is sufficient and the transaction is signed. Then it fires.
That openness has sharp edges, though. No customer support will reverse a phishing scam. No regulator will refund you if a smart contract has a bug. July 2023: the Curve hack drained roughly $70 million through a Vyper compiler reentrancy bug (whitehats clawed most back, but about $20 million stayed gone). November 2025: Balancer V2 lost $128.6 million to a rounding-direction error inside its pool invariant math. Permissionlessness hands you the right to participate. It also strips off the safety net wrapped around a permissioned system.
Real Examples Where Permissionless Mattered
Abstract values become very concrete the moment a system gets stress-tested. A few examples from recent years show exactly what the property buys you.
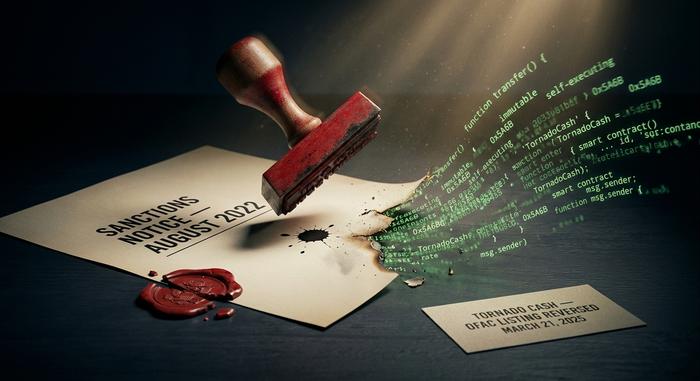
August 2022. OFAC sanctioned the Tornado Cash smart contract, an Ethereum mixer that Treasury tied to over $7 billion in alleged laundering. The sanctions made it illegal for U.S. persons to touch the contract. The contract, deployed on Ethereum, kept running anyway. No central operator could pull a switch because there was no central operator. November 2024: the 5th Circuit ruled that immutable smart contracts cannot be classified as sanctionable property. Treasury delisted Tornado Cash on March 21, 2025. The whole arc is probably the cleanest demonstration of what permissionless means in practice. The law had to bend around the code, not the other way around.
Early 2024. OFAC-compliant block builders briefly produced more than 80% of Ethereum blocks. Real concerns appeared about censorship creeping in at the validator level. The community shipped research and tooling — SUAVE, inclusion lists — that dragged the share back below 30% by 2026. Permissionlessness was not automatic here. It had to be defended.
FTX, late 2022. Customers could not move their funds because the exchange held their private keys. Anyone holding self-custodied crypto on a permissionless chain? No disruption. Their access never depended on FTX's permission to start with. "Not your keys, not your crypto" stopped being a slogan that week. It became a structural lesson.
Geographic blocks tell another piece of the story. A centralized exchange blocks users in sanctioned countries, those users are out. A permissionless DeFi protocol cannot block them at the contract level, even when the front-end tries. Most front-ends now do region-block. The contracts underneath stay open to anyone with a wallet. That gap between the friendly UI and the underlying protocol is exactly where permissionlessness lives.
Why Enterprises Pick Permissioned Chains Instead
Crypto attaches a lot of cultural weight to permissionlessness. But plenty of serious enterprise blockchain work happens on permissioned systems, and the reasons are practical. Ideology has very little to do with it.
Compliance comes first. A bank running cross-border settlements has to know its counterparties. It has to log every transaction for regulators. It has to prove no sanctioned entity has touched the rail. Permissioned chains like R3 Corda or Hyperledger Fabric bake those requirements straight into the access layer. KYC becomes a precondition for joining, not a bolt-on at the wallet level.
Performance is the second driver. Hyperledger Fabric can hold 1,000 to 3,000 TPS under realistic conditions with sub-second finality. Bitcoin tops out near 7 TPS. Ethereum L1 sits around 15-30 TPS, and L2 rollups push effective throughput into the thousands. For high-volume internal settlements, a permissioned chain often wins on latency and predictability alone.
Real deployments confirm the pattern. SWIFT's blockchain pilot for cross-border payments connects more than 30 financial institutions on a permissioned ledger. London Stock Exchange Group has been building a fully blockchain-powered trading system. Hitachi runs procurement smart contracts on Hyperledger Fabric across about 3,500 suppliers. The Walmart-IBM Food Trust uses Hyperledger Fabric with 300+ suppliers, cutting mango traceability from 7 days to 2.2 seconds. JPMorgan's Kinexys network (formerly Onyx) handles institutional settlements internally and now processes more than $5 billion per day, with cumulative volume over $3 trillion. None of these would gain anything from anonymous validators sitting in unknown jurisdictions.
The real divide is not "good permissionless vs evil permissioned." It is whichever trust model the use case actually needs. Public money, open coordination, censorship resistance? Permissionless. Internal banking infrastructure with regulatory reporting? Permissioned. Most serious institutions in 2026 keep exposure to both, depending on the workflow.
Permissionless Trade-offs: Speed, Privacy, Trust
Permissionless systems pay a real cost for being open. So before you assume "permissionless" wins every use case, look at the trade-offs.
Throughput is the obvious one. More independent validators verifying every transaction means more network propagation overhead. Bitcoin's 10-minute block time is a deliberate call. It picks settlement security over speed. Ethereum's 12-second slots are faster but still nowhere near a centralized database. L2s like Arbitrum and Base do lift effective throughput substantially, but they inherit security from a permissionless L1, and that L1 stays the bottleneck.
Privacy is cost number two. Every transaction on Bitcoin or Ethereum is public forever. Anyone can trace funds. Anyone can link addresses to real-world identities via chain analysis. Anyone can reconstruct your financial history if they really want to. Privacy-preserving permissionless tools do exist — Monero, Zcash, zk-rollups — but they sit at the margins. Permissioned chains, by contrast, can default to selective disclosure, sharing data only with authorized parties.
Predictable fees are another loss. Gas on Bitcoin and Ethereum spikes hard during congestion. Some user trying to settle a $50 transfer can eat $20 in fees during a memecoin frenzy. Permissioned chains run inside a single business, so fees are typically internalized or fixed by contract.
Trust shifts. It does not vanish. On a permissioned system you trust the operators. On a permissionless one you trust the code, the validators, and the economic incentives. Code has bugs. Validators can collude. Incentives can break. The permissionless promise is not "no trust required." It is "no single party required."
Governance of Permissionless Blockchains in 2026
A network without a CEO. So how does it decide anything? Off-chain governance, mostly. And it stays messy on purpose.
Bitcoin and Ethereum both run on improvement proposals plus public discussion plus rough consensus among developers, node operators, validators or miners, and users. No formal vote at the protocol layer, anywhere. Change ships once most stakeholders adopt the new client. If a meaningful minority refuses, the chain splits. 2016 Ethereum DAO fork. 2017 Bitcoin Cash fork. 2022 Merge. Same pattern, three very different stories.
Some newer chains bolt on on-chain governance, letting token holders vote directly on protocol parameters or treasury spending. Tezos picked that route. So did the Cosmos Hub and the 115+ app-chains hooked together through Cosmos's IBC standard. Polkadot's parachain ecosystem now spans 216 projects, each running its own governance setup. Token-weighted voting carries a real downside, though. Whales accumulate power. The Federal Reserve's 2024 note flagged this exact question as open research. Does flexible formal governance beat Bitcoin's deliberate stability? Or lose to it?
Most permissionless networks settle into a hybrid. Off-chain coordination tackles the heavy calls. On-chain voting handles narrow parameter changes. Foundations and dev organizations like the Ethereum Foundation, the Solana Foundation, and Polkadot's Web3 Foundation coordinate funding and standards. None of them actually controls the protocol code.
End state? Slower than a private company can move. Faster than any national legal system can legislate. Different metabolism, same target: keep a permissionless network coherent without breaking the property that makes it permissionless to start with.
How to Use Permissionless Crypto Tools
You probably use permissionless crypto tools already without thinking about it. The mechanics get easy once the conceptual layer clicks.
Three things, that's it. A self-custody wallet (MetaMask, Phantom, Rabby) holding your private keys on your own device. A small balance of the chain's native gas token (ETH, SOL, BTC) to pay transaction fees. The address of whatever contract or service you want to use, plus an honest read on what it actually does. No signup. No email confirmation. No waiting around for approval.
Typical permissionless flow looks like this. Open the wallet. Connect to a dApp — Uniswap, Aave, OpenSea, pick one. The dApp asks the wallet to sign a transaction. You read what it would do on the wallet screen and either approve or reject. Transaction fires, or it does not. The dApp never gets control of your funds, ever. The smart contract on-chain executes the trade or loan or NFT mint. Once enough confirmations clear, you are done.
The hardest part isn't technical. It's the discipline that openness demands. Nobody is going to stop you from clicking through a phishing transaction. Nobody is going to reverse a self-inflicted swap into some scam token. Nobody recovers your funds if you leak your seed phrase. The same property handing you the right to participate without asking removes the safety rails baked into permissioned systems. New users? Start small. Use audited protocols. Verify every address on the hardware wallet screen. Treat the seed phrase as the most sensitive object you own.